Archive
Shielded VM’s: Virtualization security is a major investment area in Hyper-V 2016
 SECURITY – Protecting the company data should be a priority.
SECURITY – Protecting the company data should be a priority.
Protecting a Virtual Machine(VM) guest from a possible host compromised as well as the certain that on a 3rd party hosting environment your VM will be protected in addition to the protection applied to the hosts is a major investment area in Hyper-V 2016.
If you find that Microsoft is helping you and your business and find it has amazing technologies as I as do, please help me out by recommending it on Recomazing a new tech platform where socially connected networks store and share trusted recommendations. Please click here to help our community.
Taking into consideration that a VM is a file, stored somewhere on a storage on locally in the Hyper-v host, it needs to be protected from attacks to the storage system, the network, while it is backed up or taken or copied to other systems.
To help protect against compromised fabric, Windows Server 2016 Hyper-V introduces Shielded VMs. A Shielded VM, requires a VM to be created as generation 2, which has a virtual TPM, is encrypted using BitLocker and can only run on healthy and approved hosts in the fabric. So, if someone copy either maliciously or accidentally the VM to a non-approved host, the VM (which is encrypted), won’t start and cannot be used to be mounted to allow access to it’s file system.
Shielded VM’s use several features to make it harder for Host administrators and malware on the host to inspect, tamper with, or steal data from the state of a shielded virtual machine. Data and state is encrypted, Hyper-V administrators can’t see the video output and disks, and the virtual machines can be restricted to run only on known, healthy hosts, as determined by a Host Guardian Server.
A configured Shielded VM has:
- BitLocker encrypted disks
- A hardened VM worker process (VMWP) that helps prevent inspection and tampering
- Automatically encrypted live migration traffic as well as encryption of its runtime state file, saved state, checkpoints and even Hyper-V Replica files (from 2016 TP5)
- Blocked console access
- Blocked PowerShell Direct
- Blocked Guest File Copy Integration Components
- Blocked services that provide possible paths from a user or process with administrative privileges to the VM.

Image Source: Microsoft – https://technet.microsoft.com/en-us/library/mt599611.aspx
With the release of Windows Server 2016 TP5, the Hyper-V team at Microsoft made shielded virtual machines compatible with Hyper-V Replica. As with copying/moving the VM, to replicate a shielded VM, the host you want to replicate to must be authorized to run that shielded VM.
The Host Guardian Service supports two different deployments of a Guarded fabric (attestation modes): TPM-trusted attestation (Hardware based) and Admin-trusted attestation (AD based).
I hope you walk away with a better understanding of the Hyper-V Shielded VM solution from this post.
Identity Management and People Ready business
Nowadays we often see an increasing business requirements to promote the integration between their applications. I’ve seen that happening a lot in the construction, education and health industries where integration and collaboration are essential to enhance an increase in productivity, but it is happening across all industries.
Identity, productivity and management are converging and with customers moving to cloud, hybrid identity is the new control plane for the enterprise allowing users to access applications with a single identity.
Identity is the peace that is common across productivity tools and apps, be it on-premise or cloud apps.
Identity and Access Management is also the key to work more effectively with remote employees, external partners and across business units. However, all too often this leads to an increase of business risks and challenges due to:
- isolated technology initiatives being deployed to solve point in time issues
- inadequate planning and identity strategy, as well as,
- ineffective controls in managing the internal and external identities to ensure privacy and legal and regulatory requirements.
An Identity and Access Management solution should:
- Be business-driven,
- Provide real business value with concrete benefits by reducing cost and improving productivity
- Improve awareness to the business, resulting in reduced dependence on support with facilities like automated workflows, self-service portals and delegated administration.
- Be able to reduce the business risk, eliminating multiple identity stores and multiple administration points, providing a single administration point and the ability to present multiple data views from a single identity store, reducing replication and synchronization while providing Single Sign-On, Security and compliance fulfillment
Identity and Productivity
To be successful in their work employees need an efficient and intuitive way to access the business applications and better collaborate, while the business needs to ensure that collaboration is taking place within the bounds of internal and external regulations, business policy, process and security.
Identity in an End-to-End Scenario
Inside the corporate network users can access all the applications they need. But how can they have access when they’re not at work?
A successful Identity Management solution should allow for end-to-end scenarios that complement business technology investments. It should allow the business to grant or block users access to sensitive applications to/from outside their physical boundaries. It should also enable users and partners to access corporate business applications which could be hosted outside or inside the corporate network in a selective and secure way.
With public cloud adoption sky rocking, the organizations need to ensure that cloud integration scenarios are in place as users expect to work from anywhere, on devices of their choice and they require access to business critical applications which could be hosted on premises or in the cloud.
Also, integrated with a client management solution, it should allow the business to block access to corporate resources when users leave the organization and/or when users’ devices are lost or stolen and the management of application access and application grant/removal access through.
Identity and Security
Identity Management solutions should address risks to critical assets by enhancing and expanding the available protections for enterprise identity. It needs to ensure it is resilient to attacks and aligns with the business security requirements. It also must identify the key components of identity management and provide effective procedures to manage security across the environment. It does not matter if it is an on-premises, a hybrid or a public cloud deployment.
The Identity Management architecture should aid as a model, be real-world, effective, consistent and manageable. It should address security, audit, confidentiality, compliance, monitoring and integrity with a centralized Identity Management repository.
Identity Strategy
The Identity strategy should be used to redesign processes and workflows, identify opportunities for automation and correct control weaknesses.
An Identity strategy can enable you to overcome challenges like
- Improving Operational Efficiency (Data/application availability, permissions, password resets)
- Reducing Security Risks (A good percentage of users recycle old passwords while others still writing them down)
- Meeting Regulation Requirements (Implementing business process/policies to meet regulations)
- Enabling Business Objectives (Improving relations with partners/customers and driving business decisions closer to LBDM’s)
Business strategy pinpoints:
– Understanding the objectives of the Identity Management solution
– Understanding the success criteria alongside which initiatives will be measured
– Overall business benefits anticipated, such as enhanced process, improved service delivery and productivity and cost reduction
– Inherent risks of the strategy, which are often related to reengineering the business processes that requires organizational changes (culturally and politically)
– Cross-organizational cooperation to implement the strategy
– Multi-Factor Authentication due to security requirements
– Application Integration
– Analytics
– Reporting
What are Microsoft’s three major investment areas for the Identity Manager vNext release?
- Hybrid scenarios that leverage cloud-based services delivered in Microsoft Azure, including Multi-Factor Authentication, Azure Active Directory application integration, analytics and reporting
- Support for the latest platforms and mobile devices with modern user interfaces
- Improved security with additional controls, analytics and auditing of administrative and privileged user identities and their access to Active Directory, Windows Server and applications
Microsoft Identity Management benefits
- Common identity. Simplify identity lifecycle management with automated workflows, business rules and easy integration with heterogeneous platforms across the datacenter and cloud. Automate identity and group provisioning based on business policy and implement workflow-driven provisioning through a single interface. Extend MIM to support new scenarios through the Visual Studio and .NET development environments.
- Enable users. Allow users to self-remediate identity issues, including group membership, smart card and password reset functions. An easy-to-use interface delivers increased productivity and satisfaction
- Protect data. Discover and map permissions across multiple systems to individual, assignable roles. Use role mining tools to discover permission sets for users across the enterprise to be later modeled and applied centrally. Increase visibility into compliance and the security state of systems across the organization with in-depth auditing and reporting
- Unify access. The Identity solution should reduce the number of usernames and passwords needed to login. Ensure admin accounts are only going where they need to go and doing what they need to do. Groups can automatically update their membership to ensure only the right people have access to your resources
Don’t wait. Get started now. Let me know how can I help you. I am looking forward to a broad and deep discussion with your business. If this is something I can help your organization then please reach me out at ac@cloudtidings.com, @cloudtidings or leave a comment here
Is Security a cloud benefit or a shared responsibility?
Cloud adoption is skyrocketing and there is no doubt about it, with more and more customers realising its benefits: costs, flexibility, availability, etc.
But how about security? Is security a cloud benefit? Well, sort of. By migrating your systems to a public cloud you certainly be assured that the providers are substantially invest on security measures, policies and certifications to guarantee the underlying infrastructure is a safe place for you to store your data and run your applications. But it stops there.
The conversation you should be having with your cloud provider is not if they are secure. They are! They have all the industry standards and certifications to guarantee that. What you should be asking is if they have real-time data, metric and resources to enable and help you to protect your company data.
The security boundaries are limited to the infrastructure of the public cloud. It is your business responsibility to make sure that your application runs safely and your data is protected and some business don’t get it.
Last week when attending a session at the MVP Summit with Brad Anderson about Identity and cloud, I realised how fragile is the conversation that is happening between organisations and the cloud providers – customers are adopting cloud with security in their mind set (In a recent study of IT decision makers by BT, more than three quarters of the respondents (76%) said that security is their main concern when it comes to cloud-based services and). But many of those customers are putting the responsibility to protect their data, solely on the public cloud provider and that is mistake that needs to be addressed.
Let’s take the example of a customer that migrated their email and documents to the cloud: among others benefits, data availability (anywhere, anytime, any device) is in my opinion one of the great cloud realisations. But the data availability also brings a security risk to organisations if they don’t invest on securing and protecting their data from non-authorised access.
Employees who access privileged company data from public Wi-Fi for example are susceptible to all sorts hackers and they have a high risk of having their device compromised. Have you thought about that? Does your company have VPN or other security measures for external access to the company data?
Also, a password only to protect someone from logon on your computer is not sufficient to protect any data you have on it. Is your company making use of solutions to encrypt the local disk? Does your company have policies in place to prevents that company data is not stored locally on your computer?
And how about your mobile? Ransomware is on the rise, with hackers taken over an entire system, holding it hostage until a fee is paid. Take the Whatsapp example – in August 2015, hackers discovered a bug that enabled them to infect devices for those utilising the web version of the app. On another example, you may recall that Lenovo faced trouble earlier this year, when it found that some of its mobiles and notebooks were sold with pre-installed spyware (According to G DATA researchers it happened somewhere along the supply chain by an outside party). The same problem happened with Huawei, Xiaomi and others.
By not having security measures on your mobile, you could let a thief to access your personal and company data if it gets stolen or lost –
- Do you have a pin to protect your mobile?
- Is your PIN strong enough or something like 1234 or 0000 or your birthday?
- If you search yourself on the internet can any of the information led to your password or PIN?
- Is your company using a device management solution?
A couple of months ago, when running a workshop to architect a solution for a customer to migrate their email to the cloud, I heard incredible the request of their IT manager: “whereas cloud concerns, the solution we want should encompass that some groups of employees should only have access to company email if they are physically connected to our network and data access should be protected from unauthorized people and devices.”.
First you will think that in the cloud times, requests to not allow the data from being accessed outside the company network would not make sense and it is a weird request, as one of the benefits of having the email in the cloud is actually being able to access it elsewhere from any device, right? But the reason is simple: they realised that migrating their email to the cloud, did not mean that their security measures and policies to protect their most precious asset: their customer’s data should not be in place. Their request was true and valid and it got me by surprise as a very few customers really understands that security in the cloud is a shared responsibility.
Security is one on the key concerns when a business decides to migrate to a public cloud and although most of them understand that the level of risk mostly relates to the behaviour and culture of their employees, some still don’t have strict policies in place and lack data access controls, which poses a high risk on their main asset: their data.
I have large experience in Security, Cloud and Datacenter Management. Reach me out and we can organize a workshop for your business at ac@cloudtidings.com
More info on the main public cloud providers security compliance:
- Microsoft For Azure : https://azure.microsoft.com/en-us/support/trust-center/
- Amazon AWS: https://aws.amazon.com/compliance/pci-data-privacy-protection-hipaa-soc-fedramp-faqs/
- VMware VCloud Air: http://vcloud.vmware.com/au/service-offering/security-overview
Hybrid Cloud Computing with Microsoft and Red Hat
Microsoft and Red Hat announced a partnership that will help customers embrace hybrid cloud computing by providing greater choice and flexibility deploying Red Hat solutions on Microsoft Azure.
 Red Hat Enterprise Linux will be the preferred option for enterprise Linux workloads on Microsoft Azure.
Red Hat Enterprise Linux will be the preferred option for enterprise Linux workloads on Microsoft Azure.
Microsoft Azure will become a Red Hat Certified Cloud and Service Provider, enabling customers to run their Red Hat Enterprise Linux applications and workloads on Microsoft Azure. Red Hat Cloud Access subscribers will be able to bring their own virtual machine images to run in Microsoft Azure.
Customers will be offered cross-platform, cross-company support spanning the Microsoft and Red Hat offerings in an integrated way, unlike any previous partnership in the public cloud. By co-locating support teams on the same premises, the experience will be simple and seamless, at cloud speed.
Red Hat CloudForms will interoperate with Microsoft Azure and Microsoft System Center Virtual Machine Manager, offering Red Hat CloudForms customers the ability to manage Red Hat Enterprise Linux on both Hyper-V and Microsoft Azure. Support for managing Azure workloads from Red Hat CloudForms is expected to be added in the next few months, extending the existing System Center capabilities for managing Red Hat Enterprise Linux
In addition, Expanding on the preview of .NET on Linux announced by Microsoft in April, developers will have access to .NET technologies across Red Hat offerings, including Red Hat OpenShift and Red Hat Enterprise Linux, jointly backed by Microsoft and Red Hat. Red Hat Enterprise Linux will be the primary development and reference operating system for .NET Core on Linux.
Cloud domain controller as a services with @Azure AD Domain Services @microsoftenterprise
That’s right Cloud AD as a services. A fully managed domain by Microsoft : Azure AD Domain Services to manage Azure IaaS workloads.
Azure AD Domain Services It’s a cloud based service which gives you a fully Windows Server Active Directory compatible set of API’s and protocols, delivered as a managed Azure service.
You don’t need to provision a Virtual Machine running Domain Controller on Azure as a IaaS anymore and have those domain controllers synchronize to their on-premises Active Directory servers using a VPN/Expressroute connection.
You can now turn on support for all the critical directory capabilities your application and server VM’s need, including Kerberos, NTLM, GROUP POLICY and LDAP.
For scenarios like Disaster Recovery and hybrid cloud deployments, it is just perfect. It means a full value of Windows Server AD in the cloud domain, without having to deploy, manage, monitor and patch domain controllers.
There are many scenarios that can be explored with this new feature.
You can enable Azure AD Domain Services for any existing Azure AD tenant – the same tenant you use with Office 365 or other SaaS applications. Azure AD Domain Services are available now.
For pricing, please check : http://azure.microsoft.com/pricing/details/active-directory-ds/
To start:
- You already deployed Azure AD Connect (to sync identity information from the on-premises Active Directory to your Azure AD tenant. This includes user accounts, their credential hashes for authentication (password sync) and group memberships)
- Create the ‘AAD DC Administrators’ group and then add all users who need to be administrators on the managed domain to it. These administrators will be able to join machines to the domain and to configure group policy for the domain.
- Configure the Network. Select or create the Azure virtual network you’d like to make domain services available in. Ensure the following:
- The virtual network belongs to a region supported by Azure AD Domain Services. See the region page for details.
- Ensure the virtual network is a regional virtual network and doesn’t use the legacy affinity groups mechanism.
- Ensure your workloads deployed in Azure Infrastructure services are connected to this virtual network
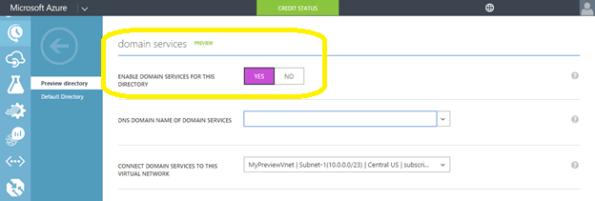
- Enable Azure AD Domain Services for your Azure AD tenant, by going to the Configure tab of your Directory, selecting Yes on ‘Enable Domain Services for This Domain’, specifying the domain name and selecting the Azure Virtual Network. Click on Save to confirm.
- Update DNS settings for the Azure virtual network to point to the new IP address of the Azure AD Domain Services you just enabled.
- Enable synchronization of legacy credential hashes to Azure AD Domain Services. This is a required step. By default, Azure AD does not store the credential hashes required for NTLM/Kerberos authentication. You need to populate these credential hashes in Azure AD so users can use them to authenticate against the domain.
A few salient aspects of the managed domain that is provisioned by Azure AD Domain Services are as follows:
- This is a stand-alone managed domain. It is NOT an extension of your on-premises domain.
- You won’t need to manage, patch or monitor this this managed domain.
- There is no need to manage AD replication to this domain. User accounts, group memberships and credentials from your on-premises directory are already synchronized to Azure AD via Azure AD Connect.
- Since the domain is managed by Azure AD Domain Services, there is no Domain Administrator or Enterprise Administrator privileges on this domain.
Microsoft TechNet Update #Brisbane : Internet of Things, Windows 10 and Microsoft Cloud OS. Free event
This is a one day event filled with the latest on Microsoft technologies broken down into 2 streams. The first stream will be all about Windows 10 and the second stream will focus on the Cloud OS and Azure. The agenda for the day is below!
| 9:00am – 10:00am | Keynote – Getting to the value of the Internet of Things | |
| 10:00am – 10:30am | Break | |
| Stream 1 – Windows 10 | Stream 2 – Microsoft Cloud OS | |
| 10:30am – 11:30am | Windows 10 – What does the new OS mean for Enterprises? | Microsoft Azure Active Directory |
| 11:40am – 12:40pm | Windows 10 – IoT | Extending Enterprise Networks to Azure using ExpressRoute |
| 12:40pm – 1:30pm | Lunch | |
| 1:30pm – 2:30pm | Windows 10 for Mobile Devices: What’s Next? | Foundation for the Software Defined Datacenter |
| 2:40pm – 3:40pm | Windows 10 – Deployment | Getting started with Microsoft Azure IaaS |
| 3:50pm – 4:50pm | Windows 10 Security – What’s new? | Windows Azure Pack Overview |
| 5:00pm – 5:15pm | Close, survey & prize draw | |
|
*Please note that this agenda is subject to modifications at any time prior to the event date. All registered attendees will be notified of any such changes. |
||
Event Details
Date: Tuesday September 24th 2015 Registration: Please click here to register for this event Location: Pullman Hotel King George Square Brisbane
What are your prefered Operations Manager Management Pack? What are the TOP 5?
The System Center community is large and continually growing. For new users that are just getting to grips with the new software, there is an abundance of additional management packs that need to be installed before getting the full benefit. These Management Packs (MPs) take the form of updates from Microsoft, free software from 3rd party vendors, and paid-for solutions from 3rd party vendors.
We want to know what your top 5 must-have MPs are in each category. Whether you are an IT Manager, Administrator, consultant, or MVP, this is your chance to share your experience and let others know what MP’s everyone should have. We will publish the results in a later blog highlighting the top 5 System Center MPs. Whether you are a new user with Microsoft System Center or a seasoned professional, the survey is completely anonymous
N.B. All Management Packs included were available on Microsoft Pinpoint or Microsoft Technet at time of writing: Vendor Management Packs, Microsoft Management Packs
Matthew Carr
Posted by Savision https://www.savision.com/resources/blog/vote-your-top-system-center-management-packs
Azure BootCamp in Brisbane: We’re heading for the big day! Join us.
We’re heading for the big day. Come and join us. This will be a one day deep dive Azure sessions held on Saturday, 2nd May.
A conference for learning about Microsoft Azure right here in Brisbane. Saturday, 2nd May 2015 – 9:00am – 5:00pm
The location will be at Microsoft, 400 George Street, Level 28.
Event Organizers: Alessandro Cardoso, Daniel Toomey and Damien Berry
Our sponsors: Microsoft, Mexia and Readify will ensure that we have resources to bring in high profile speakers
Notes:
- Given the requirement to set up tables, we must limit the attendance to 50* persons. Therefore, if you RSVP and then find you are unable to attend, please change your RSVP so that another party will have the opportunity.
– Because this event is on a Saturday, lifts will be locked. Please arrive within the 30 minute window prior to start time so we can activate the lift for you. Latecomers will not be able to gain access.
Event Website: http://tinyurl.com/BrisbaneAzureBootcamp2015
Demystifying service management’s role in private cloud by MVP Steve Buchanan
A fellow MVP Steve Buchanan and Savision just launched a new whitepaper regarding Service Management and the Private cloud. The whitepaper sets out to define private cloud, the layers of private cloud, and those layers within which service management operates. It also explores having ultimate visibility into your organization’s business services. Business services discussed in this paper consist of configuration items (CIs), monitoring, and application maps; they are underpinned with incident, change management, and modern day self-service. In addition, the whitepaper explores the integration between Operations Manager and Service Manager, and the role Savision Live Maps plays in this area.
You can download it here: http://www2.savision.com/l/12082/2015-01-16/q32vf
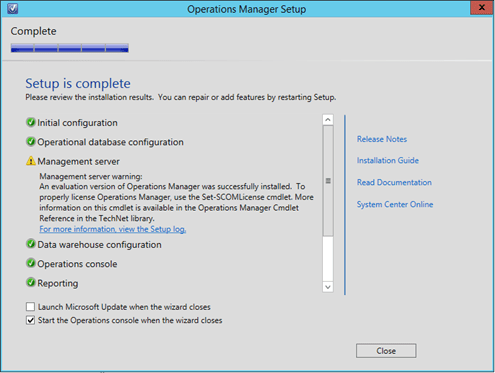
Deploying System Center Operations Manager vNext
Recently Microsoft released the preview version of their next release of Windows Server, Hyper-V and System Center as did Savision with Live Maps for System Center.
Note: This blog post was first published here : http://www.savision.com/resources/blog/installing-system-center-opsmgr-vnext-and-savision-live-maps-part-i-mvp-alessandro
You can download System Center vNext Preview here and Savision Live Maps from here.
To start, make sure of the following:
- You installed the SQL Server 2014 as the database server for the System Center vNext preview edition. To note, I run into SQL connectivity issues when I tried to use an SQL 2012 version, with a message stating that I did not have a compatible version of SQL installed. Whereas the documentation says that SQL 2012 is supported for vNext preview it is not the case.
- If the SQL Server is installed on a dedicated machine (recommended), that the host firewall is configured to allow inbound connections on port 1433 (SQL) , 80(http) and 443 (https)
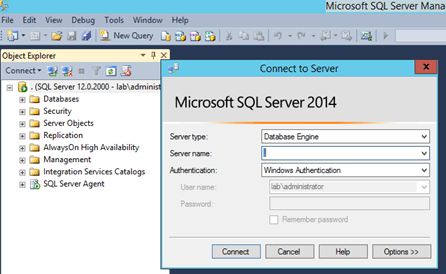
- You installed Reporting Services (SSRS), Analysis Services and Full Text Search as it is required by Operations Manager.
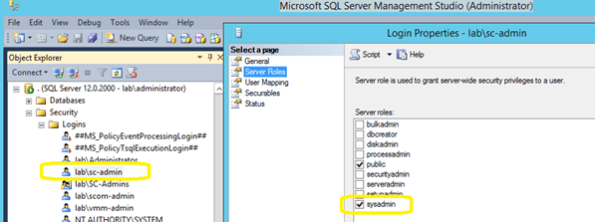
- You created an account to install System Center and it is member of local administrators. For this post, I created an account named “sc-admin”.
- Logon on the machine you plan to install System Center with the “sc-admin”
-
The “sc-admin” account has permissions to create a database in the installed SQL server. You can achieve this by either adding the account to the SQL server administrators when install SQL Server, of by adding the account using SQL Server Management Studio, by expanding Security->Logins and then creating a new login, adding the “sc-admin” account and selecting “sysadmin” as permission under Server Roles (preferable). You can also, if security is a concern, create a OperationsManager database and give the account DB Owner (dbo) permission.
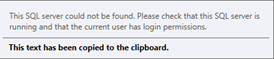
If the credentials you are using to install do not have permission to create the database you will receive the following message:
-
The SQL Server Agent is started and set to automatic:
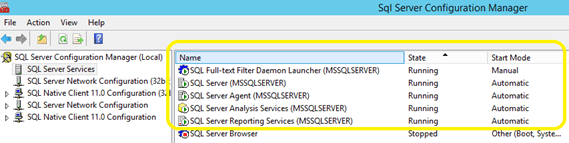
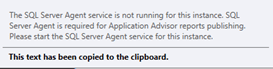
Or else the following error will appear when the Reporting Services configuration times come in the Operations Manager installation wizard.
Quick Note: You will notice that although you are installing System Center Operations Manager vNext, the initial screen will show 2012R2 🙂
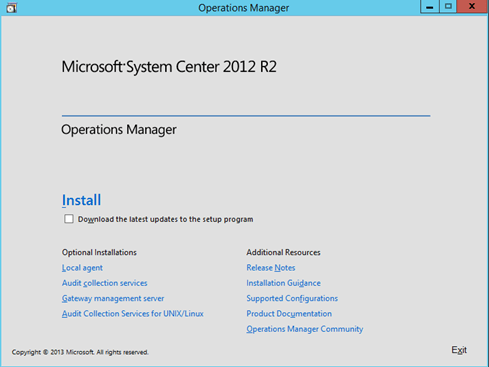
-
To initiate the installation, click on Install and the Preview logo will appear
I also recommend selecting the Download the latest updates to the setup program checkbox.
-
Select the System Center features you want to install. For this post, I am selecting: Management Server, Operations Console and Reporting Server. Click Next to continue.
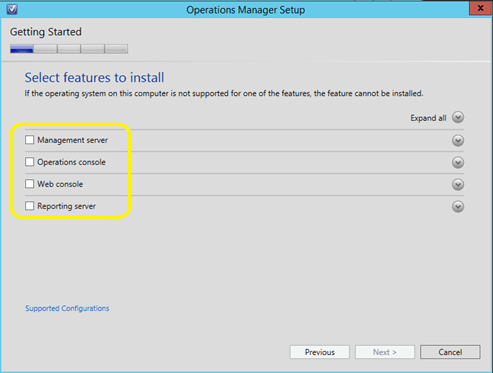
-
In the Select Installation location, provide the path for Operations Manager installation and click on Next.
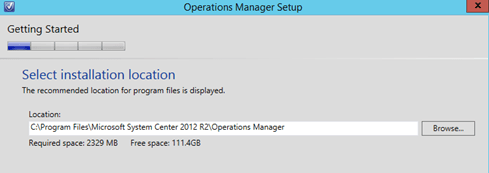
-
Your system will now be checked for hardware and software against System Center requirements. If some requirements are missing it will appear on the screen for your resolution.
The below example, Report Viewer is missing. To fix the issue, click on the
 to expand
to expand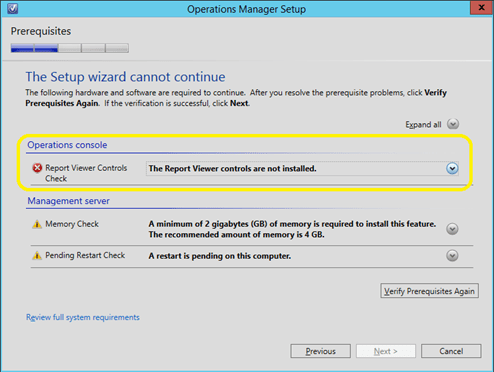
Note that in the above example there are two warnings: the first one about the system not having the recommended 4GB of memory and the second one about a pending restart. As I am installing this for a demo purpose, I can safely ignore the 1st warning, but I will have to click on Cancel and restart the machine in order to proceed the installation.
Click on the link to download and install Report Viewer
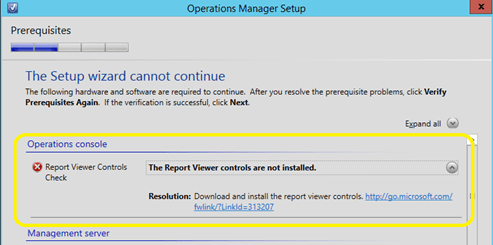
- If no error is reported, click on Next to continue.
-
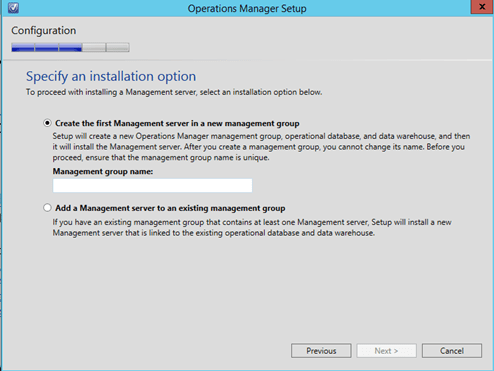
In the Specify the installation option, select Create the first Management server in a new management group and provide the name. For this post I am using the name “lab” for the management group name.
-
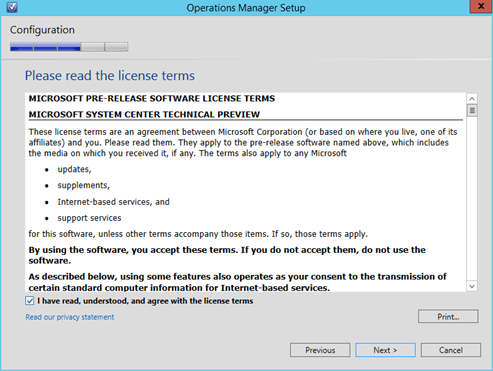
Click on Next to continue and accept the License terms and click on Next to proceed.
-
In the configure operational database, type the SQL server name and port (if different for the default 1433)
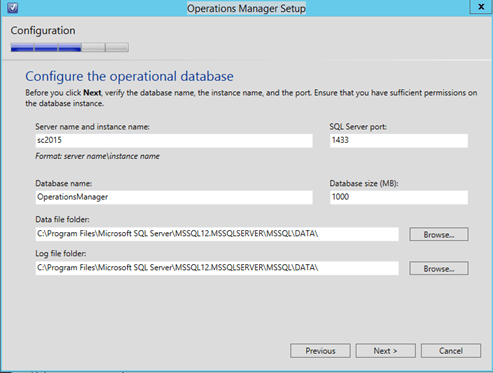
-
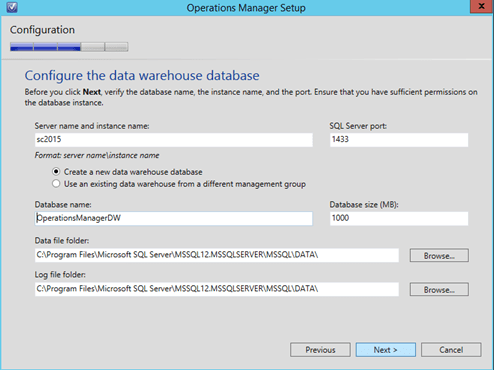
Click on Next to progress and to the next step where you will need to provide the Data Warehouse database configuration
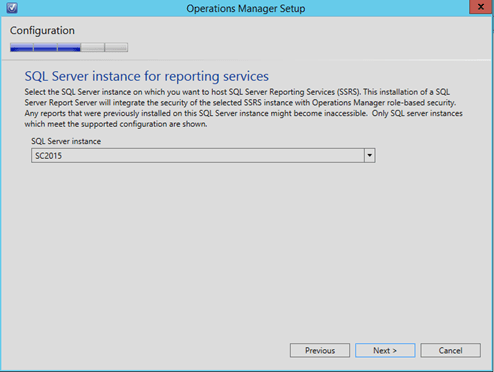
- Click on Next to continue and in the next step confirm the SQL Server instance that is running the SQL Reporting Services and then click on Next to proceed.
-
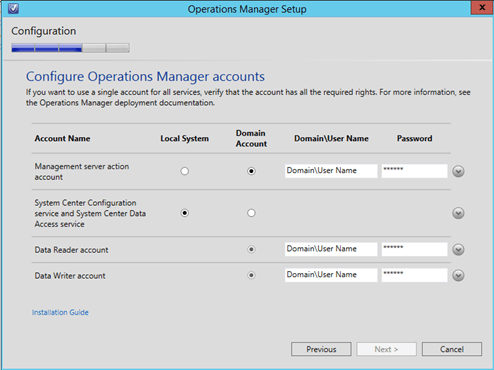
In the Configure Operations Manager accounts, provide the accounts details and click on Next to proceed.
-
In the Help improve Operations manager, select the desired options and click on Next to proceed.
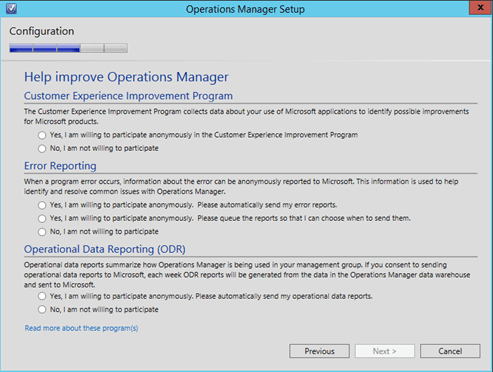
-
In the Update screen select the desired option (On is recommended) and click on Next to proceed.
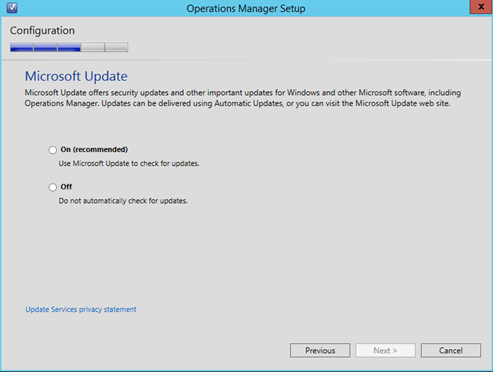
-
On the Installation Summary, click on Install and wait for the installation to complete.
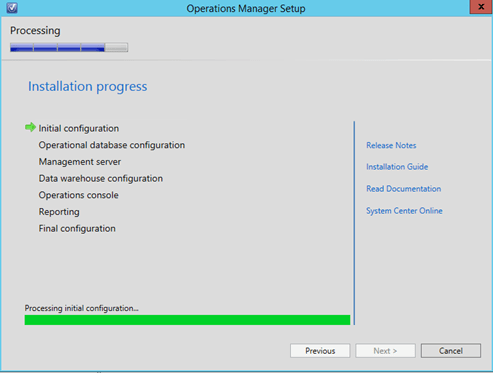
Now we have System Center Operations Manager successfully installed.