Archive
The transition to adopting cloud services is unique for every organization. What does yours look like?
- Andy Syrewicze (Microsoft MVP and Technical Evangelist – Altaro),
- Didier Van Hoye (Microsoft MVP and Infrastructure Architect – FGIA),
- Thomas Maurer (Microsoft MVP and Cloud Architect – itnetX)
There are limited seats, REGISTER NOW to save your spot
For a FREE LIVE Webinar with will focus on cloud technologies and presented as a panel-style discussion on the possibilities of cloud technologies coming out of Microsoft, including:
- Windows Server 2019 and the Software-Defined Datacenter
- New Management Experiences for Infrastructure with Windows Admin Center
- Hosting an Enterprise Grade Cloud in your datacenter with Azure Stack
- Taking your first steps into the public cloud with Azure IaaS
After watching the experts discuss the details, you’ll see that the cloud doesn’t have to be an all or nothing discussion. This webinar will prepare you for your journey by revealing the available options and how to make the most out of them!
It is a great opportunity to ask industry experts as they share their experiences working with many customers worldwide.
WHEN:
Wednesday June 13th 2018 – Presented live twice on the day
- Session 1: 2pm CEST – 5am PDT – 8am EDT
- Session 2: 6pm CEST – 9am PDT – 12pm EDT
- Twitter: https://goo.gl/f8v9mH
- Facebook: https://goo.gl/wDe7vN
- LinkedIn: https://goo.gl/go5JpL
Granting Guest or Partner users access to your on-premises apps
In the past, in order to grant guest or partners users access to on-premises applications, would require a very complicated setup and would also incur on management overhead with Trusts, VPN and guest/partners accounts being created on the local Active Directory.
Fortunately, that’s past.
Nowadays, we can grant access to Guest or Partner users to applications hosted on-premises or in the cloud. How can that be done? Simple : using the Azure B2B feature:
- For apps that use SAML-based authentication:
- Integrate the SAML app by using the non-gallery application template, as described in Configuring single sign-on to applications that are not in the Azure Active Directory application gallery. Make sure to note what you use for the Sign-on URL value.
- Use Azure AD Application Proxy to publish the on-premises app, with Azure Active Directory configured as the authentication source. The high level steps are:
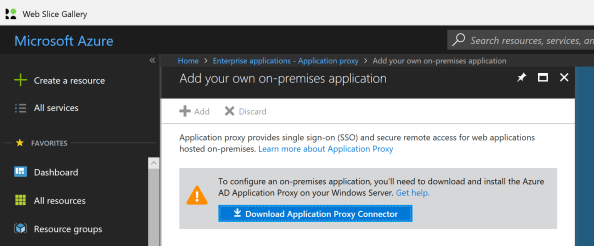
- Install the Application Proxy Connector (go to Get started with Application Proxy and install the connector)
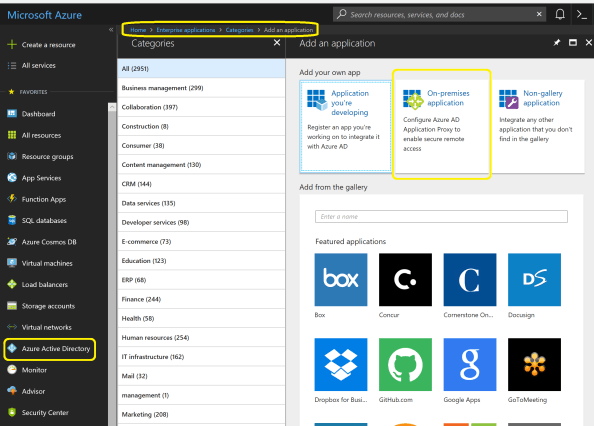
- In the Azure Portal, select on Azure Active Directory -> Enterprise Applications -> Overview, then click on +New Application

- Click on On-Premises Application
- Provide the following information application:
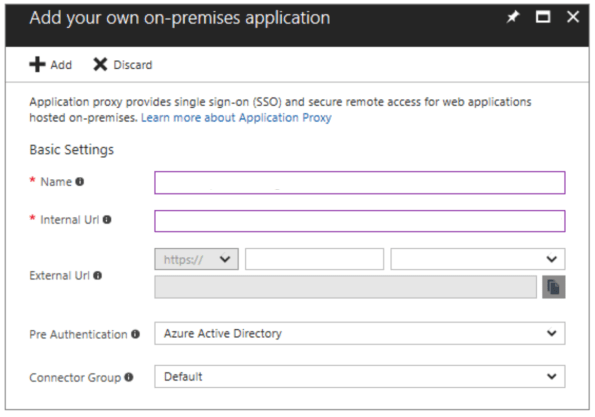
Name: The name will show on the access panel and in the Azure portal.
Internal URL: The URL that you use to access the application from inside your private network.
External URL: The address your users will go to in order to access the app from outside your network.
Pre Authentication: How Application Proxy verifies users before giving them access to your application: Azure Active Directory (default); Multi-Factor Authentication; Passthrough.
Connector Group: Connectors process the remote access to your application, and connector groups help you organize connectors and apps by region, network, or purpose.
- Install the Application Proxy Connector (go to Get started with Application Proxy and install the connector)
- For apps that use Integrated Windows Authentication (IWA) with Kerberos constrained delegation (KCD): using Azure AD Proxy for authentication. However, for authorization to work, a user object is required in the on-premises Windows Server Active Directory. There are two methods you can use to create local user objects that represent your B2B guest users:
- You can use Microsoft Identity Manager (MIM) 2016 SP1 and the MIM management agent for Microsoft Graph.
- You can use a PowerShell script. (This solution does not require MIM.)
For more information on Publishing applications with Application Proxy see https://docs.microsoft.com/en-au/azure/active-directory/manage-apps/application-proxy-publish-azure-portal
Remove yourself as guest user of a partner organisation AD tenant
In the past, when working with partner organisations where you were invited to access shared resources or applications, in order to get your access removed/revoked you would need to contact their Global Admin and ask them to remove you. That was not an easy task!
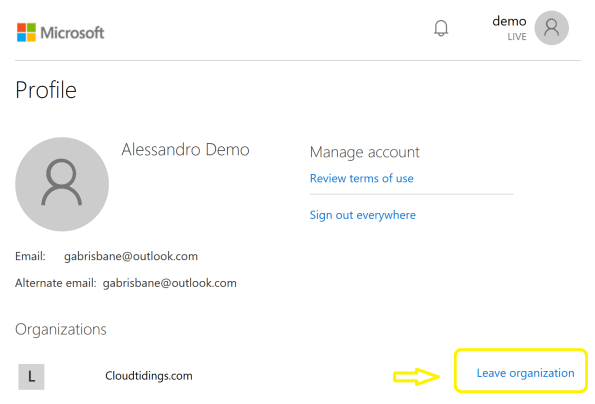
Now, Microsoft released a Azure B2B update which will allow you to remove yourself from the partner organisation AD tenant
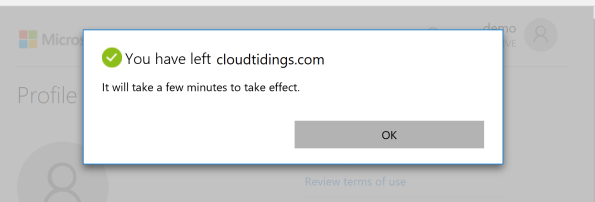
When a user leaves an organization, the user account is “soft deleted” in the directory.
By default, the user object moves to the Deleted users area in Azure AD but is not permanently deleted for 30 days. This soft deletion enables the administrator to restore the user account (including groups and permissions), if the user makes a request to restore the account within the 30-day period.
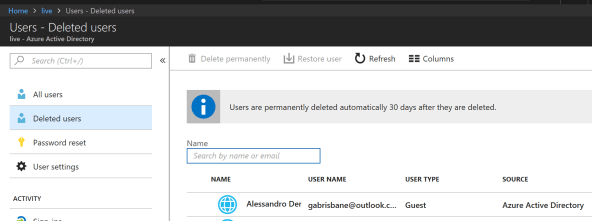
If you permanently delete a user, this action is irrevocable.
These highly-requested capabilities simplify and modernize your collaboration. They also empower your partner users and help you with your GDPR obligations.
You can find more information about this an other new exciting features of Azure B2B at : https://docs.microsoft.com/en-au/azure/active-directory/active-directory-b2b-leave-the-organization
If you’re interested in viewing or deleting personal data, please see the Azure Data Subject Requests for the GDPR article. If you’re looking for general info about GDPR, see the GDPR section of the Service Trust portal.
New Azure B2B Invite process.
 New Azure B2B Invite process: Redemption through a direct link
New Azure B2B Invite process: Redemption through a direct link
“Just in Time Redemption”.
In the past, in order for your guest/partner users to access a shared resources utilising Azure B2B Collaboration, they would have had to be invited by email to access resources/apps on your Azure Tenant. When receiving the email, your guest/partner clicks on the invitation link which will trigger its acceptance and consequent adding the guest/partner account as a guest user in your tenant and the providing access to the resources or apps you have configured.
Now, although that option still available, your guest/partner users can simply access the application you’ve invited them to. How? You can invite a guest/partner user by sending him/her a direct link to a shared app.
NEW Modernized Consent Experience. When a guest/partner user accesses your organization’s resources for the first time, they will interact with a brand new, simple, modernized consent experience.
 Image source:https://cloudblogs.microsoft.com/enterprisemobility/2018/05/14/exciting-improvements-to-the-b2b-collaboration-experience/
Image source:https://cloudblogs.microsoft.com/enterprisemobility/2018/05/14/exciting-improvements-to-the-b2b-collaboration-experience/
After any guest user signs in to access resources in a partner organization for the first time, they see a Review permissions screen.
The guest/partner user must accept the use of their information in accordance to the inviting organization’s privacy policies to continue
Upon consent, the guest/partner users will be redirected to the application shared by you.
How it works:
-
-
- You want your guest/partner user to access a specific application
- You add them as a guest user to your organization (In the Azure Portal, go to Azure Active Directory -> Users -> New Guest User)
-

- In the message invitation, type the link to the application you want them to have access to
- Now, your guest/partner user will only have to click on the link to the application to immediately access it after giving consent.
It’s very simple isn’t it?




