Archive
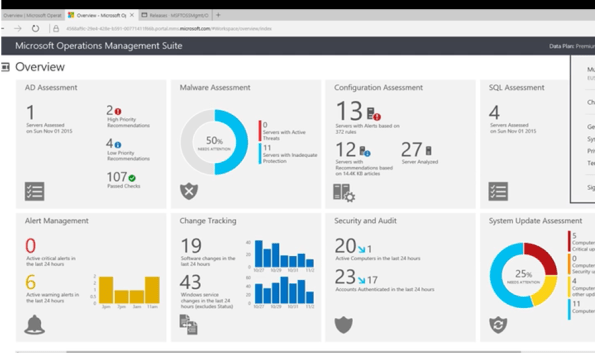
Simplify Data Center Management with Microsoft Operations Manager Suite
Modern data centers need extra care with simplified management and strong analytical capabilities to predict and prevent disasters that would have a negative business impact on your organization. Savision’s published a whitepaper, written by Microsoft MVP Janaka Rangama, focuses on monitoring Linux workloads with OMS for analytics, proactive monitoring and resource utilization in your heterogeneous data center environment.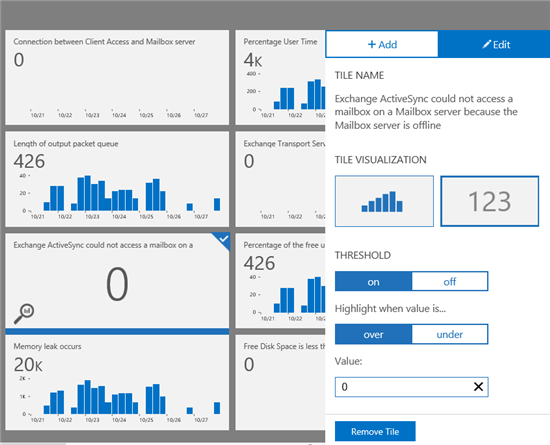
Monitoring Exchange Workloads in OMS
Learn how to simplify your datacenter management in Savision’s new whitepaper, entitled: ‘Born in the Cloud: Monitoring Linux Workloads with OMS’. The whitepaper provides insights on how organizations can combine the existing System Center Operations Manager (SCOM) environments with OMS.
Find out how to gain control over modern hybrid clouds and how to extend OMS with business service management information.
This whitepaper will focus on:
- What is Microsoft Operations Management Suite? How can it simplify data center management?
-
How can you leverage OMS Log Analytics to analyze, predict and protect your Linux workloads?
-
How can you integrate System Center Operations Manager with OMS for extended monitoring?
-
How can you harness the power of Business Service Management using Savision Live Maps Unity and Microsoft OMS?
Download the whitepaper now and learn how you can directly know how all that detailed log data impacts your business and service levels. You can download your copy of the whitepaper here: bit.ly/1NfEagJ
Security: Impunity leads to cyber crime to operate widely free in Brazil
There are evidences that Brazilian cyber criminals are cooperating with the Eastern European gangs involved with ZeuS, SpyEye and other banking Trojans, sharing know-how and exchanging favours.

With almost no legislation and very few arrests, the Brazilian cyber-criminals are motivated on ripping off their own fellow nationals and local businesses.
Sadly, the Brazilians are bracing for another tough year. With a high level of corruption in all levels of the government, no investments in education and with an legislation from the stone age, the cyber criminals have the certain of no punishment and are making many victims.
See 6 tips for staying safer online
A global survey conducted by ESET revealed that between January and November 2015, Brazil had the highest levels of global spread of some of the major banking Trojans, corresponding for 82% of all global detections of the TrojanDowloader.Banload, 72% of the Spy.Bancos and 52% of the Spy.Banker.
In 2014 Brazil was ranked the most dangerous country for financial cyber-attacks. As shocking as it sounds, sensitive data about almost every Brazilian citizen in the open.
As a safe measure, make sure you check the source of the document before you click and download it to your device – The Win32 / TrojanDownloader.Banload is a family of malware that focuses on breaking into the security solutions and perform download other malicious code aimed at stealing bank details.
To minimize the risks, at the personal level, make sure you use strong passwords, don’t share personal information on social network and use multi-authentication factor allied with an updated anti-virus and host firewall.
Many of these malicious codes are based on social engineering and pose as a trusted document in order to deceive their victims – This particular threat (Win32 / TrojanDownloader.Banload) pretends to be an Office document, however, has a double extension .docx_.scr. Its propagation occurs, especially through e-mails, where users believe that this is a Word document, when it is actually an executable file.
No matter your size or the size of your organisation. No one is too small to be a target for cyber criminals.
Do you think that you are safe here in Australia or anywhere in the world? The cyber criminals have no borders. According to the ESET Virus Radar, the number 1 threat is the Win32/Bayrob, followed by the JS/Exploit.Agent.NKZ.
My personal note to you: Start 2016 by making sure your systems are up to date, that you have an anti-virus and host firewall installed and updated and that you follow the basics of security. Visit the Microsoft Safety and Security Center at https://www.microsoft.com/security/default.aspx
If you interested in learn more about the cyber crime, there is an interesting white paper published by Trend Micro, which I recommend.
Sources:
- http://www.welivesecurity.com/2015/05/07/cpl-malware-brazil-white-paper-now-available/
- https://securelist.com/files/2015/11/KLReport_CyberUnderground_Brazil_eng.pdf
- https://www.trendmicro.com/cloud-content/us/pdfs/security-intelligence/white-papers/wp-ascending-the-ranks.pdf
- http://www.virusradar.com/?utm_source=virus_radar&utm_medium=infohub&utm_campaign=virus_radar
Image: Freedigitalphotos/Stuart Miles
Azure ASR’s SLA-backed enhanced VMware to Azure solution is now ready to replicate your on-premises workloads to Azure
You heard right. Microsoft has launched an enhanced version of its Azure Site Recovery (ASR) targeted especially for VMware customers.
The concept of ASR is very simple: organisations will be able to replicate their VMware virtual machines (VMs) to Azure, update and then run them in Azure as a disaster recovery option. They will be charged a small amount by VM but won’t have to pay for compute or storage until the VM is up and running in Azure.
To note, Azure Site Recovery, as part of Microsoft Operations Management Suite (OMS), enables your organisation to gain control and manage your workloads no matter the source: Azure, AWS, Windows Server, Linux, VMware or OpenStack.
Some of the key ASR characteristics:
- With non-disruptive recovery testing, you can easily test the failover of your VMware virtual machines to Azure within minutes, and validate your workload’s performance in Azure, without impacting on-going replication or the production workload.
- With ASR-integrated failback, start replicating your Azure virtual machines back to your on-premises ESXi environment, and failback to the original or an alternate location when your on-premises site is once again available for use.
- Heterogeneous workload support, automated VMware vCenter Server discovery
- Continuous data protection (CDP), one-click failovers with ASR Recovery Plan
- Rich health monitoring and e-mail notifications.
I’ve been working with ASR for a while and I definitely recommend it.

Source:https://azure.microsoft.com/en-us/documentation/articles/site-recovery-vmware-to-azure-classic/
Ready to start using ASR? Check out additional product information, to start replicating your workloads to Microsoft Azure using Azure Site Recovery today. You can use the powerful replication capabilities of Site Recovery for 31 days at no charge for every new physical server or virtual machine that you replicate.
You can read the announcement at https://azure.microsoft.com/en-us/blog/ga-enhanced-migration-and-disaster-recovery-for-vmware-virtual-machines-and-physical-servers-to-azure-using-asr/
Technologies that work together to create Microsoft’s SDN solutions
With the upcoming Windows 2016 and System Center 2016, there will be many technologies that will work together to create Microsoft’s Software Defined Networking (SDN) solutions and the best part is that you can already check them by downloading and deploying Windows 2016 and System Center 2016 Technical Preview.
- Hyper-V Network Virtualization, which enables virtualization of tenant networks on top of a shared physical network infrastructure. , which are being performed by hardware appliances (such as load balancers, firewalls, routers, switches, and so on) are increasingly being virtualized as virtual appliances. Microsoft has virtualized networks, switches, gateways, NATs, load balancers, and firewalls.
- Network Controller, which provides a centralized, programmable point of automation to manage, configure, monitor, and troubleshoot virtual and physical network infrastructure in your datacenter.
- RAS Gateway for High Availability and failover, which can be deployed in multitenant mode to provide network traffic routing to and from virtual and physical networks, including the Internet.
- Software Load Balancing (SLB) for SDN, which can be used to evenly distribute tenant and tenant sub-networks traffic among virtual network resources. The Windows Server SLB enables multiple servers to host the same workload, providing high availability and scalability.
- Datacenter Firewall. A new service. It is a network layer, 5-tuple (protocol, source and destination port numbers, source and destination IP addresses), stateful, multitenant firewall. When deployed and offered as a service by the service provider, tenant administrators can install and configure firewall policies to help protect their virtual networks from unwanted traffic originating from Internet and intranet networks.
- Remote Direct Memory Access (RDMA) and Switch Embedded Teaming (SET). When you use a converged NIC to combine both RDMA and Ethernet traffic using a single network adapter, it will help you reduce the capital expenditures that are associated with each server in your datacenter, because you need fewer network adapters to manage different types of traffic per server. The converged NIC allows you to use a single network adapter for management, Remote Direct Memory Access (RDMA)-enabled storage, and tenant traffic. SET is a NIC Teaming solution that is integrated in the Hyper-V Virtual Switch. SET allows the teaming of up to eight physical NICS into a single SET team, which improves availability and provides failover.
- Border Gateway Protocol (BGP). When configured Border Gateway Protocol (BGP) provides you with the ability to manage the routing of network traffic between your tenants’ VM networks and their remote sites. BGP reduces the need for manual route configuration on routers because it is a dynamic routing protocol, and automatically learns routes between sites that are connected by using site-to-site VPN connections.
- System Center. VMM can be used to deploy Software Defined Networks
Source: https://technet.microsoft.com/en-us/library/mt590952.aspx




