Archive
New features in the Remote Desktop Client RDC 7.0
The RDC 7.0 client can be used to connect to legacy terminal servers or to remote desktops as before. However, the new features that are mentioned in this article are available only when the client connects to a remote computer that is running Windows 7 or Windows Server 2008 R2
Web Single Sign-On (SSO) and Web forms-based authentication
For security, Web SSO requires remote applications to be signed using a certificate from a trusted issuer.
Access to personal virtual desktops by using RD Connection Broker
Access to virtual desktop pools by using RD Connection Broker
Status & disconnect system tray icon
RD Gateway-based device redirection enforcement
RD Gateway system and logon messages
RD Gateway background authorization & authentication
RD Gateway idle & session time-outs
NAP remediation with RD Gateway
Windows Media Player redirection
Bidirectional audio
Multiple monitor support
Note For connections with multiple monitor support enabled, AeroGlass support is currently not supported and will be turned off.
Enhanced video playback
Functionality available only when connecting from Windows 7 to Windows 2008 R2
Language Bar docking
RemoteApp allows users to use their docked Language Bar with their RemoteApp applications just as they do with the local applications.
This productive functionality was previously unavailable. Instead, users had to use the floating Language bar.
Remote application task scheduler
Remote application task scheduler functionality automatically starts remote applications on the Remote Desktop client required by the user. The client computer must have Windows 7 installed to use this feature.
Aero Glass support
Terminal Services in Windows Server 2008 did not support Aero Glass remoting for sessions. This is now supported in Windows Server 2008 R2 Remote Desktop Services, but is incompatible with multi-monitor support.
Start applications and desktops from ‘RemoteApp and Desktop Connections
Users can subscribe to all of their RemoteApp programs and desktops which are then listed in their local Start menu. The list is automatically updated as items are added or deleted
Update for Windows Vista, x86-based versions

Download the Update for Windows Vista for x86-based systems package now. (http://www.microsoft.com/downloads/details.aspx?FamilyId=ac7e58f3-2fd4-4fec-abfd-8002d34476f4)
Update for Windows Vista, x64-based versions

Download the Update for Windows Vista for x64-based systems package now. (http://www.microsoft.com/downloads/details.aspx?FamilyId=11e7a081-22a8-4da7-a6c5-cdc1ac51a1a4)
Update for Windows XP, x86-based versions

Download the Update for Windows XP for x86-based systems package now. (http://www.microsoft.com/downloads/details.aspx?FamilyId=72158b4e-b527-45e4-af24-d02938a95683)
SCVMM : Windows 7 Template Creation Error : –2147024864
Here are the Release Notes from the RC that discusses this issue. It’s about half way down under the System Preparation Tool section
http://download.microsoft.com/download/F/D/B/FDBFC5A5-51CD-4C8D-9F18-7BCC3810498E/Windows%207%20RC%20Release%20Notes.htm
SCVMM takes care of applying sysprep.
sysprep 1.1 is here:
http://www.microsoft.com/downloads/details.aspx?familyid=0C4BFB06-2824-4D2B-ABC1-0E2223133AFB&displaylang=en
and Server 2003 is here:
http://www.microsoft.com/downloads/details.aspx?familyid=93F20BB1-97AA-4356-8B43-9584B7E72556&displaylang=en
and XP is here:
http://www.microsoft.com/downloads/details.aspx?familyid=673A1019-8E3E-4BE0-AC31-70DD21B5AFA7&displaylang=en
But you most likely want the "Deployment Toolkit"
http://www.microsoft.com/downloads/details.aspx?familyid=3bd8561f-77ac-4400-a0c1-fe871c461a89&displaylang=en&Hash=HD%2f3UQpbIQnCaKf%2fth6Sfnc8bHXTDgeIgX6nNzQZVmYzRXFYx9%2bZHVDniseSpp6wwteVT%2bTXF6qj3bTF39cAsw%3d%3d
Moving R2 differencing disk to Windows Server 2008 : Need Hotfix
Hotfix needed to move R2 differencing disk to Windows Server 2008
In Windows Server 2008 R2 there was a minor change to the format of differencing virtual hard disks. As a result you will need to apply an update to Windows Server 2008 if you want to move differencing disks from Windows Server 2008 R2 to Windows Server 2008.
You can download this update from here:
http://support.microsoft.com/kb/971677
Note that this applies to Windows Server 2008 and Windows Server 2008 SP2 (not to Windows Server 2008 R2). If you do not have this update installed and you try to use a differencing disk created with Windows Server 2008 R2 you will receive an error message that states that the virtual hard disk is corrupted or unreadable.
Posted by Ben ( Virtual PC Guy )
http://blogs.msdn.com/virtual_pc_guy/archive/2009/10/16/hotfix-needed-to-move-r2-differencing-disk-to-windows-server-2008.aspx
Remote Desktop Load Simulation Tools : VDI Deployment sizing tool
In a server-based computing environment, all application execution and data processing occur on the server.
Storage. New version of StarWind allow Cluster Failover Active-Active
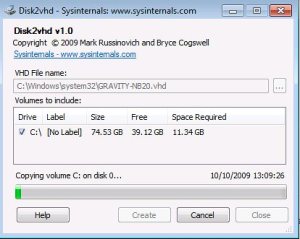
Migrating Physical Machine into Virtual Machines by using command line
- Virtual PC supports a maximum virtual disk size of 127GB. If you create a VHD from a larger disk it will not be accessible from a Virtual PC VM.
- Do not attach to VHDs on the same system on which you created them if you plan on booting from them. If you do so, Windows will assign the VHD a new disk signature to avoid a collision with the signature of the VHD’s source disk. Windows references disks in the boot configuration database (BCD) by disk signature, so when that happens Windows booted in a VM will fail to locate the boot disk.
Virtualization : Domain Controllers How to resolve Event ID 2095
If the Directory Service event log reports Event ID 2095. Here is how to fix the issue:
-
Shut down the domain controller virtual machine that recorded the error, and ensure that it does not restart.
-
Determine whether a snapshot of the domain controller was recently used as a restore mechanism. If so, this is most probably the source of the error.
-
Attempt to determine whether any changes originated from this domain controller and propagated to other domain controllers. If the event was a result of a snapshot or copy of a virtual machine being started, try to determine the time the USN rollback occurred. You can then check the replication partners of that domain controller to determine whether replication occurred since then.
You can use the Repadmin tool to make this determination. For information about how to use Repadmin, see Monitoring and Troubleshooting Active Directory Replication Using Repadmin (http://go.microsoft.com/fwlink/?LinkId=122830). If you are not able to determine this yourself, contact Microsoft Customer Service and Support (http://go.microsoft.com/fwlink/?LinkID=102491) for assistance.
-
Forcefully demote the domain controller. This involves cleaning up the domain controller’s metadata and seizing the operations master (also known as flexible single master operations or FSMO) roles. For more information, see the “Recovering from USN rollback” section of article 875495 in the Microsoft Knowledge Base (http://go.microsoft.com/fwlink/?LinkID=137182).
-
Delete all former VHD files for the domain controller.
Virtualization : Time Service Syncronization
For virtual machines that are configured as domain controllers, disable time synchronization with the host through Integration Services. Instead, accept the default Windows Time service (W32time) domain hierarchy time synchronization.
Host time synchronization makes it possible for guest operating systems to synchronize their system clocks with the system clock of the host operating system. Because domain controllers have their own time synchronization mechanism, host time synchronization must be disabled on virtual machines that are configured as domain controllers. If domain controllers synchronize time from their own source and also synchronize time from the host, the domain controller time can change frequently. Because many domain controller tasks are tied to the system time, a jump in the system time could cause lingering objects to be left in the directory and replication to be stopped.
You can disable host time synchronization in the virtual machine settings in the Integration Services section of the Hyper-V Manager by clearing the Time Synchronization check box.
Virtualization deployment practices to avoid
Virtualization platforms, such as Hyper-V, offer a number of convenience features that make managing, maintaining, backing up, and migrating computers easier. However, there are some common deployment practices and features that should not be used for virtual domain controllers. The following list describes the practices to avoid when you deploy domain controllers:
- Do not implement differencing disk virtual hard disks (VHDs) on a virtual machine that you are configuring as a domain controller. This makes it too easy to revert to a previous version, and it also decreases performance. For more information about VHD types, see New Virtual Hard Disk Wizard (http://go.microsoft.com/fwlink/?LinkID=137279).
- Do not clone the installation of an operating system without using Sysprep.exe because the security identifier (SID) of the computer will not be updated. For more information about running the System Preparation tool (Sysprep), see "Using virtual hard disks" in Ways to deploy an operating system to a virtual machine (http://go.microsoft.com/fwlink/?LinkId=137100).
- To help prevent a potential update sequence number (USN) rollback situation, do not use copies of a VHD file that represents an already deployed domain controller to deploy additional domain controllers. The next three items in this list are also recommended to help avoid potential USN rollback. For more information about USN rollback, see Appendix A: Virtualized Domain Controllers and Replication Issues.
- Do not use the Hyper-V Export feature to export a virtual machine that is running a domain controller
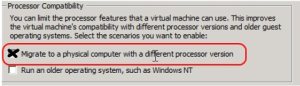
Processor Compatibility new feature of Windows 2008 R2
When a running virtual machine is moved to a server running different processor, the virtualization platform needs to provide necessary support to ensure applications running inside virtual machines continue to run on the destination processor.
The Processor Compatibility new feature of Windows 2008 R2, enables Live Migration to occur between processors at different versions/generations/steppings.
A particular Intel or AMD class of processors exists in a family. That family has multiple generations, or steppings, that define one set of processors from another. While these differences are relatively unnoticeable for most of us during our usual use of the OS, they can be enough to prevent a Live Migration from successfully occurring. The "differences" actually arrive as different processor capabilities that are baked into the chip itself.
This new feature enables the masking of these features so that a running virtual machine can successfully Live Migrate from one host to another. The result is that you must no longer be exactly equal in processor capabilities between multiple hosts. The best part is that the majority of this functionality is kept underneath the covers.
You only need to check if the box "Migrate to a physical computer with a different processor version" is marked for each VM. That’s it. The Live Migration process will eliminates concerns and conflicts and process the migration sucessfully
Scenarios
1. You have a virtual machine running on a host A and would like to be able to move it to another host B
2. You buy another server and add to the cluster. The newly added server is most likely has newly added processor features than other hosts in the cluster. You would like to be able to move running virtual machines freely from any node of the cluster.
3. You have a virtual machine running on host A, You save the VM with active memory state and would like to restore the same at a later date on any Hyper-V enabled host which may not be the same host.
How it works:
With processor compatibility mode enabled, Hyper-V only exposes the guest VM to processor features that are available across all processors of the same processor architecture, i.e. AMD-to-AMD or Intel-to-Intel. This allows the VM to be migrated to any hardware platform of the same processor architecture. Processor features are “hidden” by the Hypervisor by intercepting a VM’s CPUID instruction and clearing the returned bits corresponding to the hidden features.
When a VM in a processor compatibility mode is started following processor features are hidden from the VM:
Host running AMD based processor
SSSE3, SSE4.1, SSE4.A, SSE5, POPCNT,
LZCNT, Misaligned SSE, AMD 3DNow!,Host running Intel based processor
SSSE3, SSE4.1, SSE4.2, POPCNT, Misaligned
SSE, XSAVE, AVX
Also, VM’s cache line flush size is set to 8 bytes on AMD and Intel based hosts when in processor compatibility mode.
Important : Windows Server 2008 R2 Hyper-V will not allow migrating a VM (with or without in processor compatibility mode) from AMD based hosts to Intel based hosts, and vice versa.
VM’s processor compatibility mode is OFF by default. It can be turned on by one of the two ways:
1. Using Hyper-V Manager: from Hyper-V Manager, select CPU setting wizard of the VM.
Check a check-box labeled “Migrate to physical computer with a different processor version. You can only change this setting when VM is not running.2. Using System Center Virtual Machine Manager 2008 R2
Notes :
1. Moving down to older processer versions consider potential performance reduction due to loss of processor features which might accelerate applications performance. It’s recommended that you properly test these scenarios.
2. An application may use non-recommended methods for processor feature detection, such as instruction probing, i.e. using an exception handler and attempting to execute a feature’s instruction to determine the presence of a feature. Or, basing feature presence on the type of processor, i.e. family, model and stepping.
3. Applications may fail to launch because of the lack of a specific a processor feature It is recommended that before deploy