Archive
Shielded VM’s: Virtualization security is a major investment area in Hyper-V 2016
 SECURITY – Protecting the company data should be a priority.
SECURITY – Protecting the company data should be a priority.
Protecting a Virtual Machine(VM) guest from a possible host compromised as well as the certain that on a 3rd party hosting environment your VM will be protected in addition to the protection applied to the hosts is a major investment area in Hyper-V 2016.
If you find that Microsoft is helping you and your business and find it has amazing technologies as I as do, please help me out by recommending it on Recomazing a new tech platform where socially connected networks store and share trusted recommendations. Please click here to help our community.
Taking into consideration that a VM is a file, stored somewhere on a storage on locally in the Hyper-v host, it needs to be protected from attacks to the storage system, the network, while it is backed up or taken or copied to other systems.
To help protect against compromised fabric, Windows Server 2016 Hyper-V introduces Shielded VMs. A Shielded VM, requires a VM to be created as generation 2, which has a virtual TPM, is encrypted using BitLocker and can only run on healthy and approved hosts in the fabric. So, if someone copy either maliciously or accidentally the VM to a non-approved host, the VM (which is encrypted), won’t start and cannot be used to be mounted to allow access to it’s file system.
Shielded VM’s use several features to make it harder for Host administrators and malware on the host to inspect, tamper with, or steal data from the state of a shielded virtual machine. Data and state is encrypted, Hyper-V administrators can’t see the video output and disks, and the virtual machines can be restricted to run only on known, healthy hosts, as determined by a Host Guardian Server.
A configured Shielded VM has:
- BitLocker encrypted disks
- A hardened VM worker process (VMWP) that helps prevent inspection and tampering
- Automatically encrypted live migration traffic as well as encryption of its runtime state file, saved state, checkpoints and even Hyper-V Replica files (from 2016 TP5)
- Blocked console access
- Blocked PowerShell Direct
- Blocked Guest File Copy Integration Components
- Blocked services that provide possible paths from a user or process with administrative privileges to the VM.

Image Source: Microsoft – https://technet.microsoft.com/en-us/library/mt599611.aspx
With the release of Windows Server 2016 TP5, the Hyper-V team at Microsoft made shielded virtual machines compatible with Hyper-V Replica. As with copying/moving the VM, to replicate a shielded VM, the host you want to replicate to must be authorized to run that shielded VM.
The Host Guardian Service supports two different deployments of a Guarded fabric (attestation modes): TPM-trusted attestation (Hardware based) and Admin-trusted attestation (AD based).
I hope you walk away with a better understanding of the Hyper-V Shielded VM solution from this post.
Comparing Windows Server Networking features : W2012 x W2008.
Windows 2012 : Feature rich, extensible, all there in the box, no compromises
| Networking feature | Windows Server 2008 | Windows Server 2008 R2 | Windows Server 2012 |
| NIC Teaming | Yes, via partners | Yes, via partners | Windows NIC Teaming in box. |
| VLAN Tagging | Yes | Yes | Yes |
| MAC Spoofing Protection | No | Yes, with R2 SP1 | Yes |
| ARP Spoofing Protection | No | Yes, with R2 SP1 | Yes |
| SR-IOV Networking | No | No | Yes |
| Network QoS | No | No | Yes |
| Network Metering | No | No | Yes |
| Network Monitor Modes | No | No | Yes |
| IPsec Task Offload | No | No | Yes |
| VM Trunk Mode | No | No | Yes |
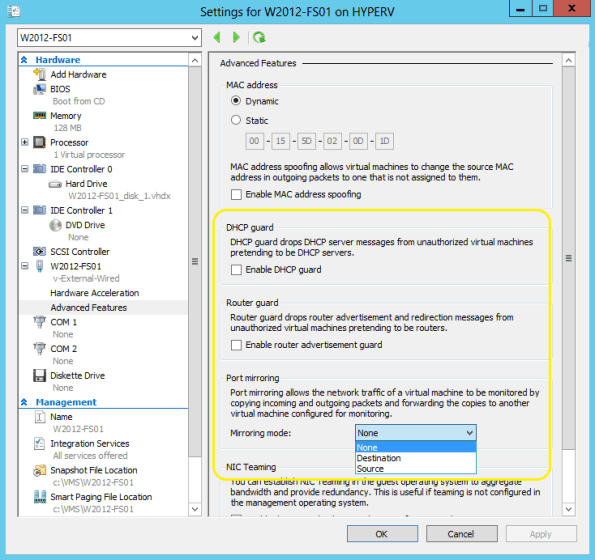
Windows 2012 Hyper-V Advanced Network Security : DHCP Guard, Router Guard, Port Mirroring
Windows 2012 Hyper-V brought a lot of new features. There are many improvements in security as well:
These settings are configured per Virtual Machine and Virtual Switch. To configure :
- Open the Hyper-V Manager and then select the Virtual Machine (e.g. W2012-FS01)
- On the right panel, click on Settings.
- Select the Virtual Switch (e.g. v-External-Wired) you want to configure and expand Advanced Features.
Find out what hotfix or update replaces other windows updates
Sometimes you need an hotfix but you find that hotfix is currently unavailable for online request. How to find out a superseding hotfix.
I found out the procedure in this wiki page : http://social.technet.microsoft.com/wiki/contents/articles/windows-server-how-to-determine-update-supersedence-and-find-replacing-hotfixes.aspx