Archive
NEW Entitlement Management: Automating employee and partner access requests, approvals and auditing
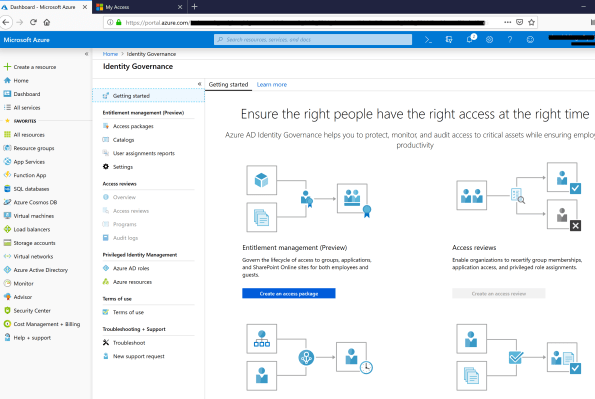
Microsoft announced today the public preview of the Entitlement Management, which is part of the Azure AD Identity Governance.
I have been working with it since Private Preview, having deployed it ona Proof of Concept for a customer in Australia, for a scenario where user onboarding with workflow approval to access applications is a critical requirement.
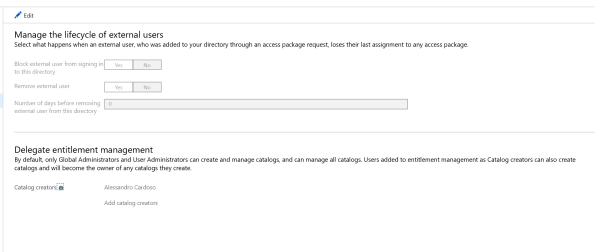
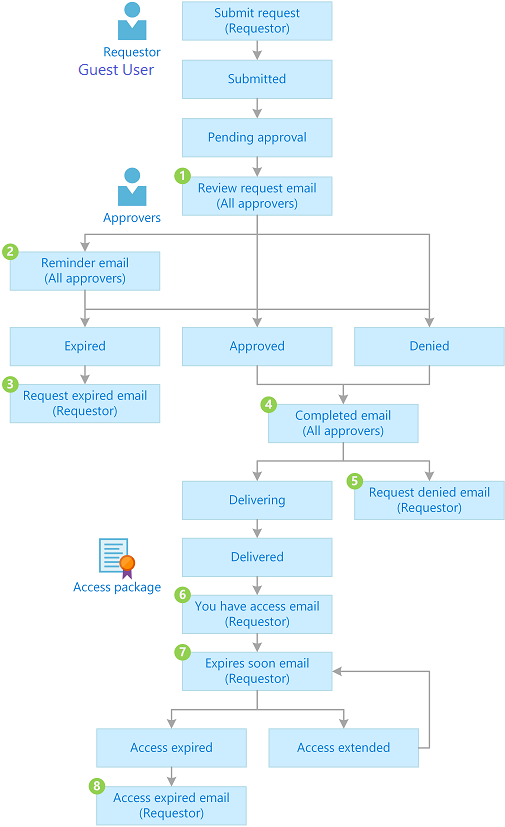
Azure AD entitlement management works with Azure AD B2B to enable collaboration across business partners. Employees from a business partner can request access to resources using the same access packages and our policy engine, including provisioning their accounts upon approval by a business sponsor. This makes it simple to grant access to a specified set of resources for your business partners while knowing your processes are compliant and secure.
Here are some of capabilities of entitlement management:
- Create packages of related resources that users can request
- Define rules for how to request resources and when access expires
- Govern the lifecycle of access for both internal and external users
- Delegate management of resources
- Designate approvers to approve requests
- Create reports to track history
To try these features in your own directory, sign in to the Azure portal as an administrator, and go to the Azure Active Directory > Identity governance section.
In summary, with the ELM preview, Azure AD now provide:
- Access request workflows, where you can configure different approval workflows for different groups of employees or guests who might request access.
- Time-limited access for groups, apps, and sites, so users who are approved don’t retain access indefinitely—their access can be set to automatically expire.
Request Workflow with approval…
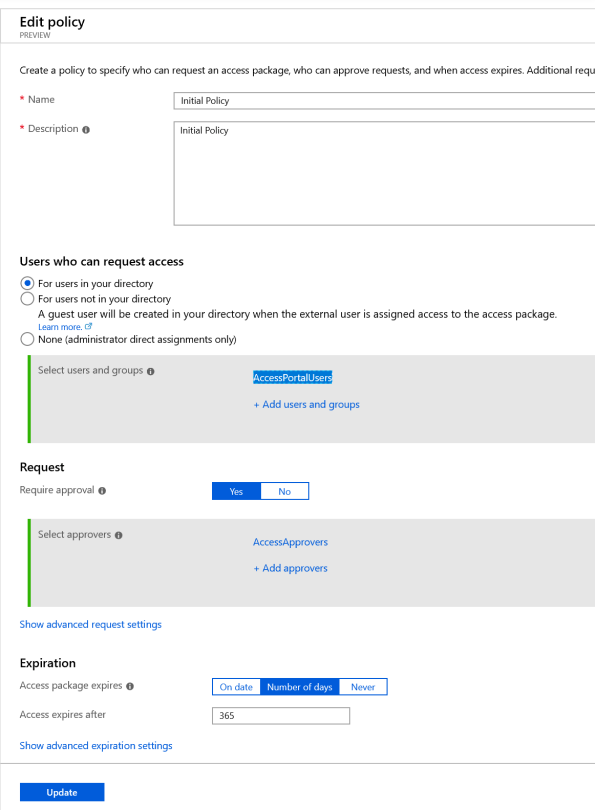
Creating a Policy …
Note: Entitlement management reaquires Azure AD Premium P2 or Enterprise Mobility + Security (EMS) E5.
For an overview of Identity Governance and entitlement management, watch the following video from the Ignite 2018 conference: https://youtu.be/aY7A0Br8u5M
For more information see https://docs.microsoft.com/en-au/azure/active-directory/governance/entitlement-management-overview
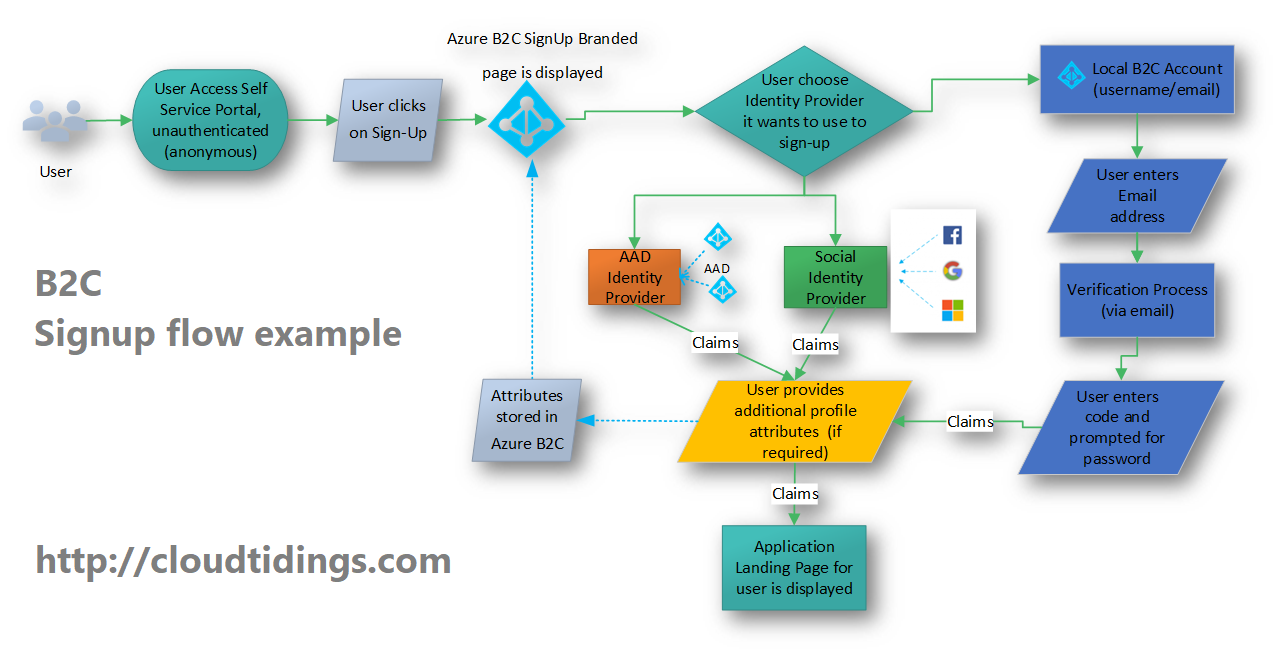
Azure B2C: Flexibility is the key
I have been working in some challenging’s Identity projects for the past 2 years and I have been amazed by the great flexibility that Azure B2C offers.
This week I am in Prague delivering an Azure Bootcamp for our
internal Microsoft team and speaking on Identity and Security and Azure B2C is one of the major points of my sessions.
In August this year I’ve completed a project that enabled a major financial institution to offer an secure and easy way for their partners/customers to sign in to access their application.
Azure Active Directory B2C is a reliable, globally-distributed service with an SLA of 99.9%, capable of supporting millions of users and billions of authentications per day, allowing users to sign in with Microsoft Accounts, Azure AD, Facebook, Google+, LinkedIn and many others, or your own Identity provider,
Customers profiles are protected through various security controls in addition to application or policy-based multi-factor authentication.
You can learn more on how to manage sign-up, sign-in, and customer profiles in your ASP.NET, desktop, or single-page Node.js applications at https://docs.microsoft.com/en-us/azure/active-directory-b2c/#step-by-step-tutorials
Remove yourself as guest user of a partner organisation AD tenant

In the past, when working with partner organisations where you were invited to access shared resources or applications, in order to get your access removed/revoked you would need to contact their Global Admin and ask them to remove you. That was not an easy task!
Now, Microsoft released a Azure B2B update which will allow you to remove yourself from the partner organisation AD tenant

When a user leaves an organization, the user account is “soft deleted” in the directory.
By default, the user object moves to the Deleted users area in Azure AD but is not permanently deleted for 30 days. This soft deletion enables the administrator to restore the user account (including groups and permissions), if the user makes a request to restore the account within the 30-day period.

If you permanently delete a user, this action is irrevocable.
These highly-requested capabilities simplify and modernize your collaboration. They also empower your partner users and help you with your GDPR obligations.
You can find more information about this an other new exciting features of Azure B2B at : https://docs.microsoft.com/en-au/azure/active-directory/active-directory-b2b-leave-the-organization
If you’re interested in viewing or deleting personal data, please see the Azure Data Subject Requests for the GDPR article. If you’re looking for general info about GDPR, see the GDPR section of the Service Trust portal.
New Azure B2B Invite process.
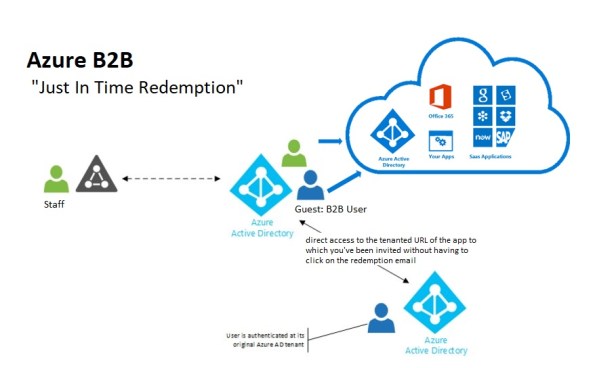 New Azure B2B Invite process: Redemption through a direct link
New Azure B2B Invite process: Redemption through a direct link
“Just in Time Redemption”.
In the past, in order for your guest/partner users to access a shared resources utilising Azure B2B Collaboration, they would have had to be invited by email to access resources/apps on your Azure Tenant. When receiving the email, your guest/partner clicks on the invitation link which will trigger its acceptance and consequent adding the guest/partner account as a guest user in your tenant and the providing access to the resources or apps you have configured.
Now, although that option still available, your guest/partner users can simply access the application you’ve invited them to. How? You can invite a guest/partner user by sending him/her a direct link to a shared app.
NEW Modernized Consent Experience. When a guest/partner user accesses your organization’s resources for the first time, they will interact with a brand new, simple, modernized consent experience.
 Image source:https://cloudblogs.microsoft.com/enterprisemobility/2018/05/14/exciting-improvements-to-the-b2b-collaboration-experience/
Image source:https://cloudblogs.microsoft.com/enterprisemobility/2018/05/14/exciting-improvements-to-the-b2b-collaboration-experience/
After any guest user signs in to access resources in a partner organization for the first time, they see a Review permissions screen.
The guest/partner user must accept the use of their information in accordance to the inviting organization’s privacy policies to continue
Upon consent, the guest/partner users will be redirected to the application shared by you.
How it works:
-
-
- You want your guest/partner user to access a specific application
- You add them as a guest user to your organization (In the Azure Portal, go to Azure Active Directory -> Users -> New Guest User)
-

- In the message invitation, type the link to the application you want them to have access to
- Now, your guest/partner user will only have to click on the link to the application to immediately access it after giving consent.
It’s very simple isn’t it?
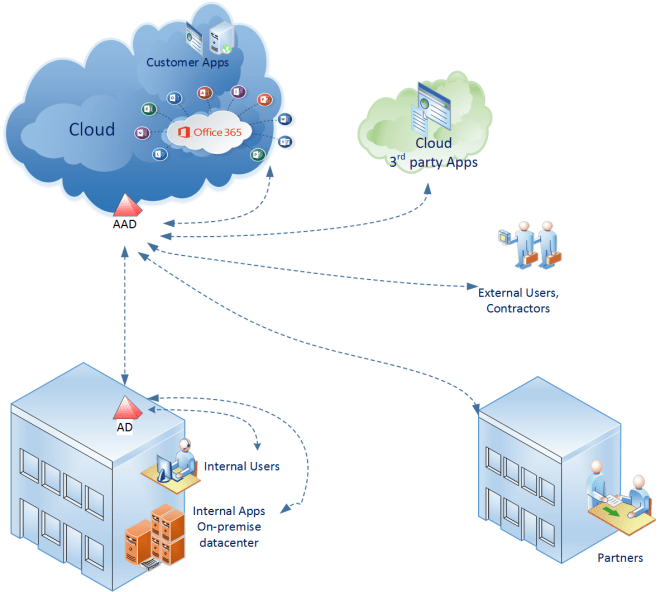
Identity Management and People Ready business
Nowadays we often see an increasing business requirements to promote the integration between their applications. I’ve seen that happening a lot in the construction, education and health industries where integration and collaboration are essential to enhance an increase in productivity, but it is happening across all industries.
Identity, productivity and management are converging and with customers moving to cloud, hybrid identity is the new control plane for the enterprise allowing users to access applications with a single identity.
Identity is the peace that is common across productivity tools and apps, be it on-premise or cloud apps.
Identity and Access Management is also the key to work more effectively with remote employees, external partners and across business units. However, all too often this leads to an increase of business risks and challenges due to:
- isolated technology initiatives being deployed to solve point in time issues
- inadequate planning and identity strategy, as well as,
- ineffective controls in managing the internal and external identities to ensure privacy and legal and regulatory requirements.
An Identity and Access Management solution should:
- Be business-driven,
- Provide real business value with concrete benefits by reducing cost and improving productivity
- Improve awareness to the business, resulting in reduced dependence on support with facilities like automated workflows, self-service portals and delegated administration.
- Be able to reduce the business risk, eliminating multiple identity stores and multiple administration points, providing a single administration point and the ability to present multiple data views from a single identity store, reducing replication and synchronization while providing Single Sign-On, Security and compliance fulfillment
Identity and Productivity
To be successful in their work employees need an efficient and intuitive way to access the business applications and better collaborate, while the business needs to ensure that collaboration is taking place within the bounds of internal and external regulations, business policy, process and security.
Identity in an End-to-End Scenario
Inside the corporate network users can access all the applications they need. But how can they have access when they’re not at work?
A successful Identity Management solution should allow for end-to-end scenarios that complement business technology investments. It should allow the business to grant or block users access to sensitive applications to/from outside their physical boundaries. It should also enable users and partners to access corporate business applications which could be hosted outside or inside the corporate network in a selective and secure way.
With public cloud adoption sky rocking, the organizations need to ensure that cloud integration scenarios are in place as users expect to work from anywhere, on devices of their choice and they require access to business critical applications which could be hosted on premises or in the cloud.
Also, integrated with a client management solution, it should allow the business to block access to corporate resources when users leave the organization and/or when users’ devices are lost or stolen and the management of application access and application grant/removal access through.
Identity and Security
Identity Management solutions should address risks to critical assets by enhancing and expanding the available protections for enterprise identity. It needs to ensure it is resilient to attacks and aligns with the business security requirements. It also must identify the key components of identity management and provide effective procedures to manage security across the environment. It does not matter if it is an on-premises, a hybrid or a public cloud deployment.
The Identity Management architecture should aid as a model, be real-world, effective, consistent and manageable. It should address security, audit, confidentiality, compliance, monitoring and integrity with a centralized Identity Management repository.
Identity Strategy
The Identity strategy should be used to redesign processes and workflows, identify opportunities for automation and correct control weaknesses.
An Identity strategy can enable you to overcome challenges like
- Improving Operational Efficiency (Data/application availability, permissions, password resets)
- Reducing Security Risks (A good percentage of users recycle old passwords while others still writing them down)
- Meeting Regulation Requirements (Implementing business process/policies to meet regulations)
- Enabling Business Objectives (Improving relations with partners/customers and driving business decisions closer to LBDM’s)
Business strategy pinpoints:
– Understanding the objectives of the Identity Management solution
– Understanding the success criteria alongside which initiatives will be measured
– Overall business benefits anticipated, such as enhanced process, improved service delivery and productivity and cost reduction
– Inherent risks of the strategy, which are often related to reengineering the business processes that requires organizational changes (culturally and politically)
– Cross-organizational cooperation to implement the strategy
– Multi-Factor Authentication due to security requirements
– Application Integration
– Analytics
– Reporting
What are Microsoft’s three major investment areas for the Identity Manager vNext release?
- Hybrid scenarios that leverage cloud-based services delivered in Microsoft Azure, including Multi-Factor Authentication, Azure Active Directory application integration, analytics and reporting
- Support for the latest platforms and mobile devices with modern user interfaces
- Improved security with additional controls, analytics and auditing of administrative and privileged user identities and their access to Active Directory, Windows Server and applications
Microsoft Identity Management benefits
- Common identity. Simplify identity lifecycle management with automated workflows, business rules and easy integration with heterogeneous platforms across the datacenter and cloud. Automate identity and group provisioning based on business policy and implement workflow-driven provisioning through a single interface. Extend MIM to support new scenarios through the Visual Studio and .NET development environments.
- Enable users. Allow users to self-remediate identity issues, including group membership, smart card and password reset functions. An easy-to-use interface delivers increased productivity and satisfaction
- Protect data. Discover and map permissions across multiple systems to individual, assignable roles. Use role mining tools to discover permission sets for users across the enterprise to be later modeled and applied centrally. Increase visibility into compliance and the security state of systems across the organization with in-depth auditing and reporting
- Unify access. The Identity solution should reduce the number of usernames and passwords needed to login. Ensure admin accounts are only going where they need to go and doing what they need to do. Groups can automatically update their membership to ensure only the right people have access to your resources
Don’t wait. Get started now. Let me know how can I help you. I am looking forward to a broad and deep discussion with your business. If this is something I can help your organization then please reach me out at ac@cloudtidings.com, @cloudtidings or leave a comment here
Cloud domain controller as a services with @Azure AD Domain Services @microsoftenterprise
That’s right Cloud AD as a services. A fully managed domain by Microsoft : Azure AD Domain Services to manage Azure IaaS workloads.
Azure AD Domain Services It’s a cloud based service which gives you a fully Windows Server Active Directory compatible set of API’s and protocols, delivered as a managed Azure service.
You don’t need to provision a Virtual Machine running Domain Controller on Azure as a IaaS anymore and have those domain controllers synchronize to their on-premises Active Directory servers using a VPN/Expressroute connection.
You can now turn on support for all the critical directory capabilities your application and server VM’s need, including Kerberos, NTLM, GROUP POLICY and LDAP.
For scenarios like Disaster Recovery and hybrid cloud deployments, it is just perfect. It means a full value of Windows Server AD in the cloud domain, without having to deploy, manage, monitor and patch domain controllers.
There are many scenarios that can be explored with this new feature.
You can enable Azure AD Domain Services for any existing Azure AD tenant – the same tenant you use with Office 365 or other SaaS applications. Azure AD Domain Services are available now.
For pricing, please check : http://azure.microsoft.com/pricing/details/active-directory-ds/
To start:
- You already deployed Azure AD Connect (to sync identity information from the on-premises Active Directory to your Azure AD tenant. This includes user accounts, their credential hashes for authentication (password sync) and group memberships)
- Create the ‘AAD DC Administrators’ group and then add all users who need to be administrators on the managed domain to it. These administrators will be able to join machines to the domain and to configure group policy for the domain.
- Configure the Network. Select or create the Azure virtual network you’d like to make domain services available in. Ensure the following:
- The virtual network belongs to a region supported by Azure AD Domain Services. See the region page for details.
- Ensure the virtual network is a regional virtual network and doesn’t use the legacy affinity groups mechanism.
- Ensure your workloads deployed in Azure Infrastructure services are connected to this virtual network

- Enable Azure AD Domain Services for your Azure AD tenant, by going to the Configure tab of your Directory, selecting Yes on ‘Enable Domain Services for This Domain’, specifying the domain name and selecting the Azure Virtual Network. Click on Save to confirm.
- Update DNS settings for the Azure virtual network to point to the new IP address of the Azure AD Domain Services you just enabled.
- Enable synchronization of legacy credential hashes to Azure AD Domain Services. This is a required step. By default, Azure AD does not store the credential hashes required for NTLM/Kerberos authentication. You need to populate these credential hashes in Azure AD so users can use them to authenticate against the domain.
A few salient aspects of the managed domain that is provisioned by Azure AD Domain Services are as follows:
- This is a stand-alone managed domain. It is NOT an extension of your on-premises domain.
- You won’t need to manage, patch or monitor this this managed domain.
- There is no need to manage AD replication to this domain. User accounts, group memberships and credentials from your on-premises directory are already synchronized to Azure AD via Azure AD Connect.
- Since the domain is managed by Azure AD Domain Services, there is no Domain Administrator or Enterprise Administrator privileges on this domain.
Cloud and Identity Access
Identity and Access
Controlling who can access which resources is key for Cloud projects. Recently I was talking with a customer that has external users (partners) and internal users and the ability to centralize and manage the access for those users is essential.
Azure provides ways for customers to federate user identities to Azure Active Directory as well as enabling Multi-Factor Authentication and the new Role Based Access Control (RBAC) features can be used to restrict access and permissions for specific cloud resources.
Monitoring
To help detect suspicious access, Azure Active Directory offers reports that alert you to anomalous activity, such as a user logging in from an unknown device. In addition, operational logging and alerting capabilities can notify customers if someone stops a website or if a virtual machine is deleted. It is possible also to use an on premise System Center Operations Manager to monitor the availability and performance of resources that are running on Windows Azure.
The reports provides up to 30 days of data representing key changes in the directory, providing the action, timestamp, the user/application that performed the action, and the user/application on which the action was performed.
Network
With new VNET-to-VNET connectivity, multiple virtual networks can be directly and securely linked to one another. In addition, ExpressRoute is now generally available, enabling customers to establish a private connection to Azure datacenters, keeping their traffic off the Internet. Building on those enhancements, Microsoft also introduced Network Security Groups for easier subnet isolation in multi-tier topologies.
Security
Azure uses industry-leading capabilities, including recent enhancements to TLS/SSL cipher suites and Perfect Forward Secrecy, to encrypt content flowing over the internet between the customer and the Azure service
Microsoft is committed to advancing cloud security with a goal to not only meet, but exceed the level of protection most enterprises have in place on-premises or in their own datacenters. For the latest information on security features and best practices, visit the Microsoft Azure Trust Center.