Archive
The transition to adopting cloud services is unique for every organization. What does yours look like?
- Andy Syrewicze (Microsoft MVP and Technical Evangelist – Altaro),
- Didier Van Hoye (Microsoft MVP and Infrastructure Architect – FGIA),
- Thomas Maurer (Microsoft MVP and Cloud Architect – itnetX)
There are limited seats, REGISTER NOW to save your spot
For a FREE LIVE Webinar with will focus on cloud technologies and presented as a panel-style discussion on the possibilities of cloud technologies coming out of Microsoft, including:
- Windows Server 2019 and the Software-Defined Datacenter
- New Management Experiences for Infrastructure with Windows Admin Center
- Hosting an Enterprise Grade Cloud in your datacenter with Azure Stack
- Taking your first steps into the public cloud with Azure IaaS
After watching the experts discuss the details, you’ll see that the cloud doesn’t have to be an all or nothing discussion. This webinar will prepare you for your journey by revealing the available options and how to make the most out of them!
It is a great opportunity to ask industry experts as they share their experiences working with many customers worldwide.
WHEN:
Wednesday June 13th 2018 – Presented live twice on the day
- Session 1: 2pm CEST – 5am PDT – 8am EDT
- Session 2: 6pm CEST – 9am PDT – 12pm EDT
- Twitter: https://goo.gl/f8v9mH
- Facebook: https://goo.gl/wDe7vN
- LinkedIn: https://goo.gl/go5JpL
System Center and Cloud Technologies showcase at SCU Australia
For the FIRST time ever, System Center Universe is coming to Australia in 2016! This is a first-class community conference where you can mingle with experts and fellow industry professionals to explore new technologies. The conference has been running for many years in Asia, typically Singapore and Malaysia and also in Europe and USA.
This one days event will be showcasing upcoming System Center solutions and Cloud Technologies with integration of the latest Windows 10!
Who should attend SCU?
System Center Universe Australia is a technical conference for administrators, engineers, architects, project managers and other technical-oriented people that are focused on Microsoft products and technologies. Less technical oriented people can still benefit from the conference by getting a broad overview of problem-solving solutions and of course by connecting to exhibitors and community specialists.
Why is SCU different from other conferences?
SCU is a first-class community conference that lives from inputs and ideas from people who are part of the community and knows about real-world requirements and solutions. That said, we are not marketing-driven but to present the latest and greatest content with the best speakers. Sessions are presented with lots of live demos and can go technically deep, mainly down to level 300 or 400 (advanced and expert). Attending SCU gives you ready-to-use knowledge and allows you to connect and build long-term relations with speakers and attendees from all over the world.
Conference Date
March 11, 2016
Conference Venue
Crown Promenade Melbourne, Australia
Conference Language
English
Is Security a cloud benefit or a shared responsibility?
Cloud adoption is skyrocketing and there is no doubt about it, with more and more customers realising its benefits: costs, flexibility, availability, etc.
But how about security? Is security a cloud benefit? Well, sort of. By migrating your systems to a public cloud you certainly be assured that the providers are substantially invest on security measures, policies and certifications to guarantee the underlying infrastructure is a safe place for you to store your data and run your applications. But it stops there.
The conversation you should be having with your cloud provider is not if they are secure. They are! They have all the industry standards and certifications to guarantee that. What you should be asking is if they have real-time data, metric and resources to enable and help you to protect your company data.
The security boundaries are limited to the infrastructure of the public cloud. It is your business responsibility to make sure that your application runs safely and your data is protected and some business don’t get it.
Last week when attending a session at the MVP Summit with Brad Anderson about Identity and cloud, I realised how fragile is the conversation that is happening between organisations and the cloud providers – customers are adopting cloud with security in their mind set (In a recent study of IT decision makers by BT, more than three quarters of the respondents (76%) said that security is their main concern when it comes to cloud-based services and). But many of those customers are putting the responsibility to protect their data, solely on the public cloud provider and that is mistake that needs to be addressed.
Let’s take the example of a customer that migrated their email and documents to the cloud: among others benefits, data availability (anywhere, anytime, any device) is in my opinion one of the great cloud realisations. But the data availability also brings a security risk to organisations if they don’t invest on securing and protecting their data from non-authorised access.
Employees who access privileged company data from public Wi-Fi for example are susceptible to all sorts hackers and they have a high risk of having their device compromised. Have you thought about that? Does your company have VPN or other security measures for external access to the company data?
Also, a password only to protect someone from logon on your computer is not sufficient to protect any data you have on it. Is your company making use of solutions to encrypt the local disk? Does your company have policies in place to prevents that company data is not stored locally on your computer?
And how about your mobile? Ransomware is on the rise, with hackers taken over an entire system, holding it hostage until a fee is paid. Take the Whatsapp example – in August 2015, hackers discovered a bug that enabled them to infect devices for those utilising the web version of the app. On another example, you may recall that Lenovo faced trouble earlier this year, when it found that some of its mobiles and notebooks were sold with pre-installed spyware (According to G DATA researchers it happened somewhere along the supply chain by an outside party). The same problem happened with Huawei, Xiaomi and others.
By not having security measures on your mobile, you could let a thief to access your personal and company data if it gets stolen or lost –
- Do you have a pin to protect your mobile?
- Is your PIN strong enough or something like 1234 or 0000 or your birthday?
- If you search yourself on the internet can any of the information led to your password or PIN?
- Is your company using a device management solution?
A couple of months ago, when running a workshop to architect a solution for a customer to migrate their email to the cloud, I heard incredible the request of their IT manager: “whereas cloud concerns, the solution we want should encompass that some groups of employees should only have access to company email if they are physically connected to our network and data access should be protected from unauthorized people and devices.”.
First you will think that in the cloud times, requests to not allow the data from being accessed outside the company network would not make sense and it is a weird request, as one of the benefits of having the email in the cloud is actually being able to access it elsewhere from any device, right? But the reason is simple: they realised that migrating their email to the cloud, did not mean that their security measures and policies to protect their most precious asset: their customer’s data should not be in place. Their request was true and valid and it got me by surprise as a very few customers really understands that security in the cloud is a shared responsibility.
Security is one on the key concerns when a business decides to migrate to a public cloud and although most of them understand that the level of risk mostly relates to the behaviour and culture of their employees, some still don’t have strict policies in place and lack data access controls, which poses a high risk on their main asset: their data.
I have large experience in Security, Cloud and Datacenter Management. Reach me out and we can organize a workshop for your business at ac@cloudtidings.com
More info on the main public cloud providers security compliance:
- Microsoft For Azure : https://azure.microsoft.com/en-us/support/trust-center/
- Amazon AWS: https://aws.amazon.com/compliance/pci-data-privacy-protection-hipaa-soc-fedramp-faqs/
- VMware VCloud Air: http://vcloud.vmware.com/au/service-offering/security-overview
Cloud domain controller as a services with @Azure AD Domain Services @microsoftenterprise
That’s right Cloud AD as a services. A fully managed domain by Microsoft : Azure AD Domain Services to manage Azure IaaS workloads.
Azure AD Domain Services It’s a cloud based service which gives you a fully Windows Server Active Directory compatible set of API’s and protocols, delivered as a managed Azure service.
You don’t need to provision a Virtual Machine running Domain Controller on Azure as a IaaS anymore and have those domain controllers synchronize to their on-premises Active Directory servers using a VPN/Expressroute connection.
You can now turn on support for all the critical directory capabilities your application and server VM’s need, including Kerberos, NTLM, GROUP POLICY and LDAP.
For scenarios like Disaster Recovery and hybrid cloud deployments, it is just perfect. It means a full value of Windows Server AD in the cloud domain, without having to deploy, manage, monitor and patch domain controllers.
There are many scenarios that can be explored with this new feature.
You can enable Azure AD Domain Services for any existing Azure AD tenant – the same tenant you use with Office 365 or other SaaS applications. Azure AD Domain Services are available now.
For pricing, please check : http://azure.microsoft.com/pricing/details/active-directory-ds/
To start:
- You already deployed Azure AD Connect (to sync identity information from the on-premises Active Directory to your Azure AD tenant. This includes user accounts, their credential hashes for authentication (password sync) and group memberships)
- Create the ‘AAD DC Administrators’ group and then add all users who need to be administrators on the managed domain to it. These administrators will be able to join machines to the domain and to configure group policy for the domain.
- Configure the Network. Select or create the Azure virtual network you’d like to make domain services available in. Ensure the following:
- The virtual network belongs to a region supported by Azure AD Domain Services. See the region page for details.
- Ensure the virtual network is a regional virtual network and doesn’t use the legacy affinity groups mechanism.
- Ensure your workloads deployed in Azure Infrastructure services are connected to this virtual network
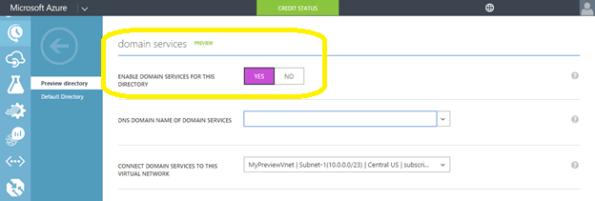
- Enable Azure AD Domain Services for your Azure AD tenant, by going to the Configure tab of your Directory, selecting Yes on ‘Enable Domain Services for This Domain’, specifying the domain name and selecting the Azure Virtual Network. Click on Save to confirm.
- Update DNS settings for the Azure virtual network to point to the new IP address of the Azure AD Domain Services you just enabled.
- Enable synchronization of legacy credential hashes to Azure AD Domain Services. This is a required step. By default, Azure AD does not store the credential hashes required for NTLM/Kerberos authentication. You need to populate these credential hashes in Azure AD so users can use them to authenticate against the domain.
A few salient aspects of the managed domain that is provisioned by Azure AD Domain Services are as follows:
- This is a stand-alone managed domain. It is NOT an extension of your on-premises domain.
- You won’t need to manage, patch or monitor this this managed domain.
- There is no need to manage AD replication to this domain. User accounts, group memberships and credentials from your on-premises directory are already synchronized to Azure AD via Azure AD Connect.
- Since the domain is managed by Azure AD Domain Services, there is no Domain Administrator or Enterprise Administrator privileges on this domain.
Is System Center Operations Manager still relevant in the Cloud?
EXCLUSIVE Whitepaper: Is OpsMgr still relevant in the Cloud by MVP Cameron Fuller
|
The addition of the Cloud has truly changed how we monitor in Microsoft solutions. In this whitepaper, Microsoft MVP Cameron Fuller tackles the elephant in the room and answers the question of the relevance of Operations Manager. Find out whether Operations Manager is still relevant in the world of the Cloud
|
Hyper-V Containers bringing speed and scale to the next level in today’s cloud-first world
Last October, Microsoft and Docker, Inc. jointly announced plans to bring containers to developers across the Docker and Windows ecosystems via Windows Server.
Hyper-V Containers will ensure code running in one container remains isolated and cannot impact the host operating system or other containers running on the same host. Applications developed for Windows Server Containers can be deployed as a Hyper-V Container without modification, providing greater flexibility for operators who need to choose degrees of density, agility, and isolation in a multi-platform, multi-application environment.

The new Microsoft Container technology offers flexibility and choice through Windows Server containers, Linux containers, and Hyper-V containers both in the cloud and on-premises.
Essence of Cloud Computing with Azure and SQL Seminar. Register Now. Free Event. [Limited seats]
I am presenting two amazing sessions showing what’s new in Hyper-V vNext and how to migrate your workloads to Azure, from VMware, AWS and Hyper-v. Don’t miss out this unique opportunity! It is time again for the annual MVP event across Asia Pacific. Register now for this Free Event. [Limited seats]
 |
|||
 |
|||
 |
|||
 |
|||
 |
|||
 |
|||
 |
|||
 |
|||
 |
|||
 |
 |
 |
 |
 |
 |
 |
 |
 |
|||
7 Years as Microsoft Most Valuable Professional
My heartfelt thanks Microsoft. Once again and for the past 7 years, I am tremendously honoured to receive the distinguished Microsoft MVP award, particularly given the select group of experts who are recognized.
A big thank you to Ben Armstrong, Sarah Cooley and the Hyper-V team.
“The Microsoft MVP Award recognizes inspiring, trusted, and independent experts from around the world who voluntarily share their passion and knowledge of Microsoft products with others.
… MVPs represent nearly 100 countries, speak over 40 different languages, and are awarded in almost 90 Microsoft technologies. Together, they answer more than 10 million questions each year.
Of the more than 100 million social and technical community members worldwide, only small portion are recognized as MVPs. As part of their award experience, MVPs are invited to share their feedback through direct interactions with Microsoft product group teams.”
I’m really looking forward to 2015 as it is promising to be a very exciting year with the release of Windows Server and System Center vNext looking to be one of the best versions ever launched.
Note sent by Microsoft:
Thank you for your exceptional contributions to technical communities! It gives us great pleasure to present you with the Microsoft Most Valuable Professional Award for the technical expertise you generously provide to others. By sharing your knowledge, experience, and objective feedback, you inspire and help people to solve problems and discover new capabilities every day. We are honored to welcome you as a Microsoft MVP.
Steven Guggenheimer
Corporate Vice President
Once again, THANK YOU! It is great to be awarded for something you love to do and it is a great motivation to continue contributing to the community.
I also would like to thank Readify for their support. If you are passionate about technology as we, Readifarians are, check out what do here: http://readify.net
Deploying System Center Operations Manager vNext
Recently Microsoft released the preview version of their next release of Windows Server, Hyper-V and System Center as did Savision with Live Maps for System Center.
Note: This blog post was first published here : http://www.savision.com/resources/blog/installing-system-center-opsmgr-vnext-and-savision-live-maps-part-i-mvp-alessandro
You can download System Center vNext Preview here and Savision Live Maps from here.
To start, make sure of the following:
- You installed the SQL Server 2014 as the database server for the System Center vNext preview edition. To note, I run into SQL connectivity issues when I tried to use an SQL 2012 version, with a message stating that I did not have a compatible version of SQL installed. Whereas the documentation says that SQL 2012 is supported for vNext preview it is not the case.
- If the SQL Server is installed on a dedicated machine (recommended), that the host firewall is configured to allow inbound connections on port 1433 (SQL) , 80(http) and 443 (https)
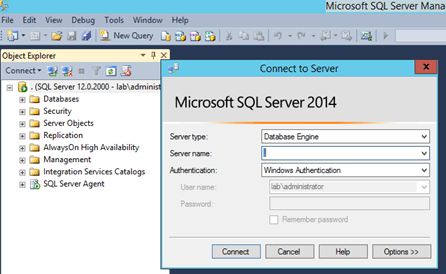
- You installed Reporting Services (SSRS), Analysis Services and Full Text Search as it is required by Operations Manager.
- You created an account to install System Center and it is member of local administrators. For this post, I created an account named “sc-admin”.
- Logon on the machine you plan to install System Center with the “sc-admin”
-
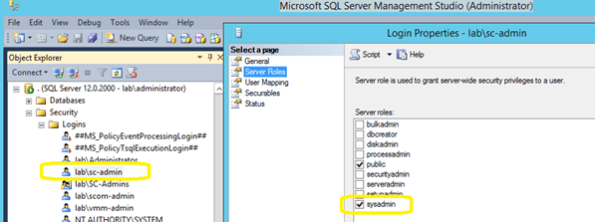
The “sc-admin” account has permissions to create a database in the installed SQL server. You can achieve this by either adding the account to the SQL server administrators when install SQL Server, of by adding the account using SQL Server Management Studio, by expanding Security->Logins and then creating a new login, adding the “sc-admin” account and selecting “sysadmin” as permission under Server Roles (preferable). You can also, if security is a concern, create a OperationsManager database and give the account DB Owner (dbo) permission.
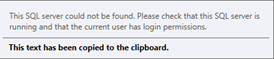
If the credentials you are using to install do not have permission to create the database you will receive the following message:
-
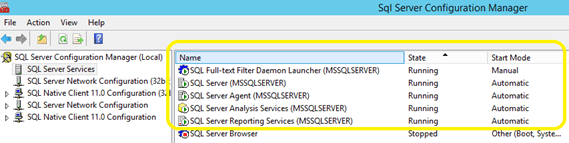
The SQL Server Agent is started and set to automatic:
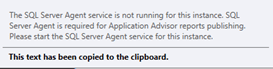
Or else the following error will appear when the Reporting Services configuration times come in the Operations Manager installation wizard.
Quick Note: You will notice that although you are installing System Center Operations Manager vNext, the initial screen will show 2012R2 🙂
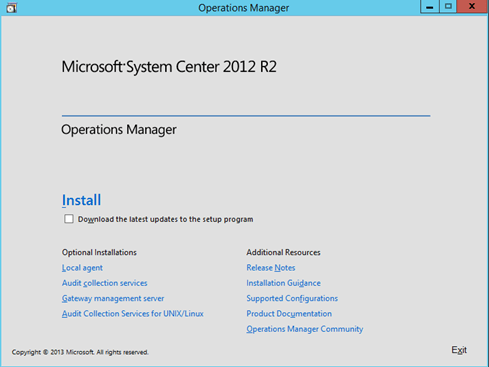
-
To initiate the installation, click on Install and the Preview logo will appear
I also recommend selecting the Download the latest updates to the setup program checkbox.
-
Select the System Center features you want to install. For this post, I am selecting: Management Server, Operations Console and Reporting Server. Click Next to continue.
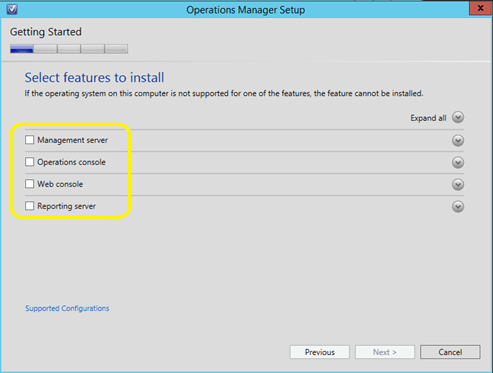
-
In the Select Installation location, provide the path for Operations Manager installation and click on Next.
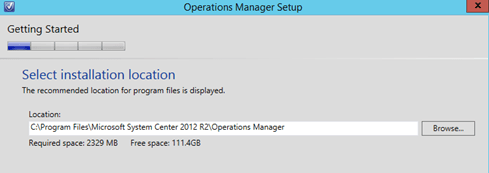
-
Your system will now be checked for hardware and software against System Center requirements. If some requirements are missing it will appear on the screen for your resolution.
The below example, Report Viewer is missing. To fix the issue, click on the
 to expand
to expand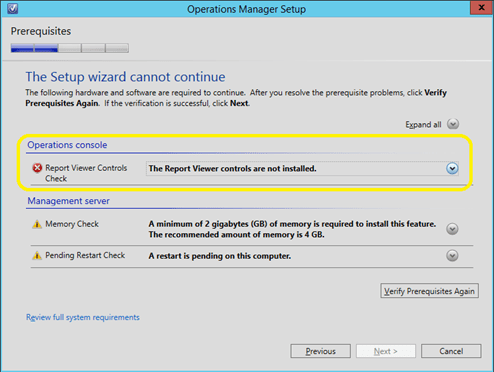
Note that in the above example there are two warnings: the first one about the system not having the recommended 4GB of memory and the second one about a pending restart. As I am installing this for a demo purpose, I can safely ignore the 1st warning, but I will have to click on Cancel and restart the machine in order to proceed the installation.
Click on the link to download and install Report Viewer
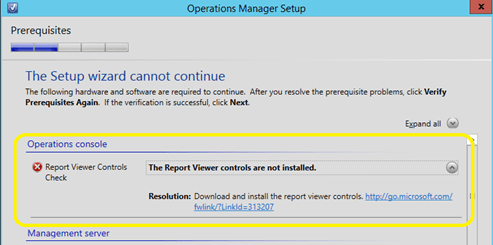
- If no error is reported, click on Next to continue.
-
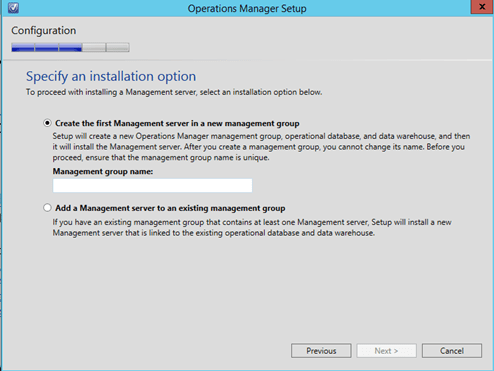
In the Specify the installation option, select Create the first Management server in a new management group and provide the name. For this post I am using the name “lab” for the management group name.
-
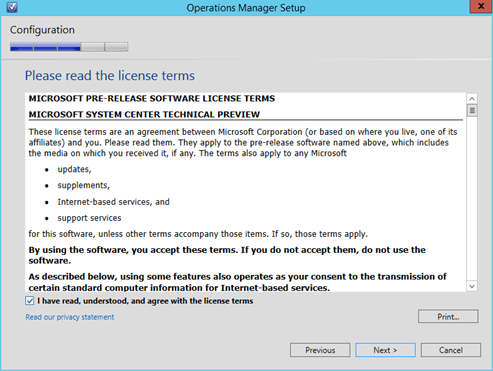
Click on Next to continue and accept the License terms and click on Next to proceed.
-
In the configure operational database, type the SQL server name and port (if different for the default 1433)
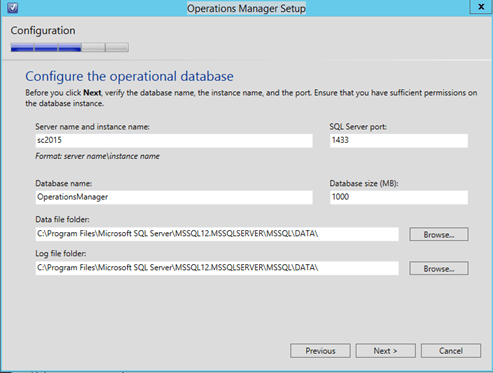
-
Click on Next to progress and to the next step where you will need to provide the Data Warehouse database configuration
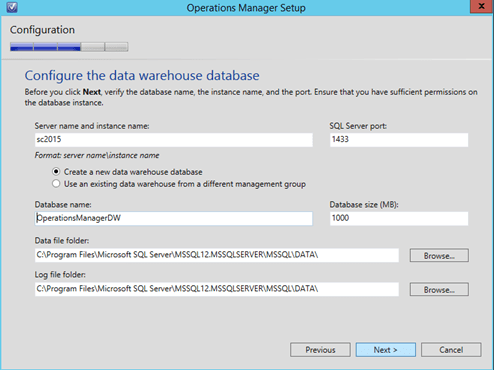
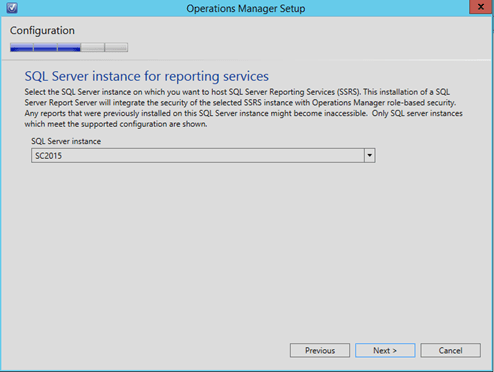
- Click on Next to continue and in the next step confirm the SQL Server instance that is running the SQL Reporting Services and then click on Next to proceed.
-
In the Configure Operations Manager accounts, provide the accounts details and click on Next to proceed.
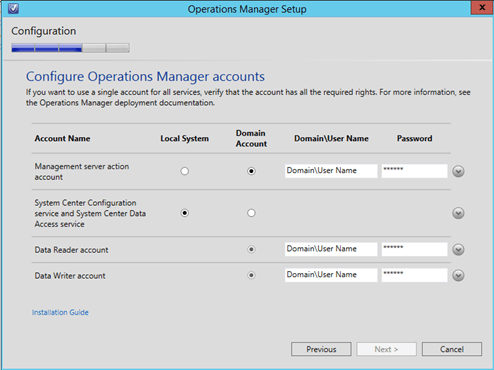
-
In the Help improve Operations manager, select the desired options and click on Next to proceed.
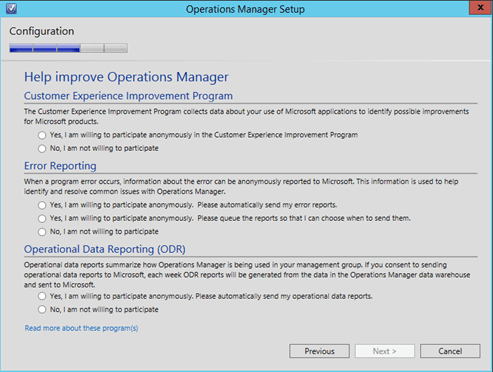
-
In the Update screen select the desired option (On is recommended) and click on Next to proceed.
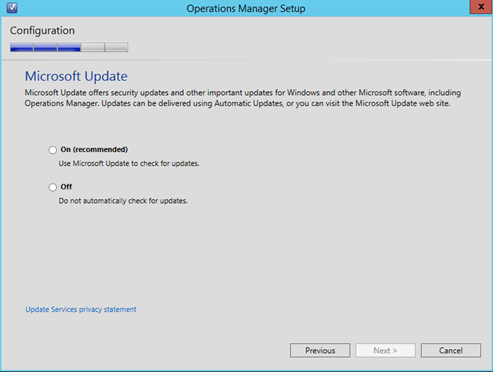
-
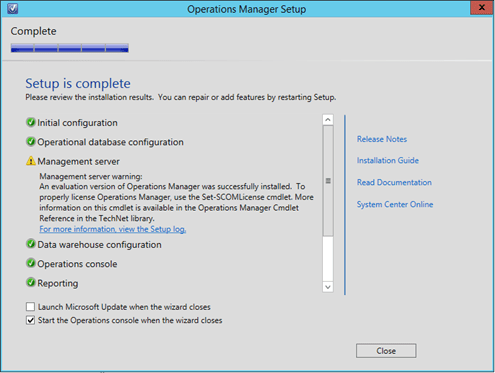
On the Installation Summary, click on Install and wait for the installation to complete.
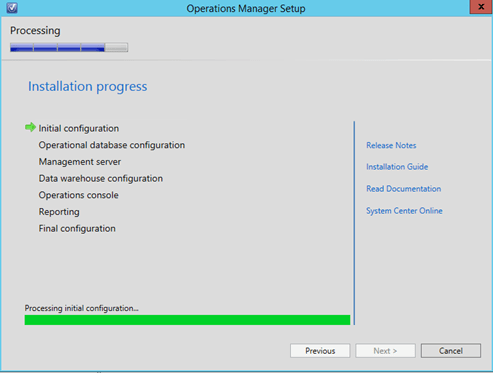
Now we have System Center Operations Manager successfully installed.
Azure RemoteApp will be generally available on December 11, 2014
Azure RemoteApp delivers Windows Server session-based applications from Azure.
Azure RemoteApp, enable users to access corporate applications from anywhere and on a variety of devices, scale up or down to meet the dynamic business needs without large capital expense or management complexity, and centralize and protect corporate applications with the security features and reliability of Azure.
Azure RemoteApp will be generally available on December 11, 2014. Azure RemoteApp instances created during the current public preview period will continue to function as they do today. These instances will automatically transition to a 30-day free trial on December 11, 2014. The limit of two app collections and 10 users per instance will continue to be enforced during the free trial period. To remove these limitations, you can exit the free trial at any point and be charged the rates detailed on the Azure RemoteApp Pricing Details webpage.
For more information, please visit the Azure RemoteApp webpage. For a comprehensive look at pricing, please visit the Azure RemoteApp Pricing Details webpage.