Archive
Which industries are most under threat, and what is the most frequently used cyberattack methods?
Examining the development of spam and advanced threats: 40% of all incoming emails pose a potential threat
Cybercrime remains one of the biggest threats worldwide, according to a new report from email cloud security and backup provider Hornetsecurity. The Cyber Threat Report Edition 2021/2022 details the latest insights and data on the current threat situation with a focus on email communication. The report examines the development of spam and advanced threats, shows which industries are most under threat, and identifies the most frequently used cyberattack methods. It also reviews the most crucial cybercrime-related events of the past year.
As the primary means of communication for business, email is one of the main gateways for cybercrime and remains a prime attack vector. Threat researchers at the Hornetsecurity Security Lab found that 40% of all inbound emails out of the total email traffic during the research period posed a potential threat. This includes spam, phishing emails, and advanced threats such as CEO fraud and any type of malware.
Phishing, malicious links, and ransomware are among the most popular attack tactics used by hackers. “Brand impersonation” is especially popular. For this, cybercriminals copy a company‘s corporate design and mimic the sender address in such a way that it can hardly be distinguished from the original, genuine email address. The main aim is to obtain the user’s access data or to spread malware via hidden links. At 16.5%, Deutsche Post and DHL are among the top five most frequently imitated brands.
In addition to this and other insights about the current state of global cybercrime, the Cyber Threat Report Edition 2021/2022 also provides an outlook on further possible developments.
Get your free copy of the Cyber Threat Report today, and access all data, figures, and visuals!
Becoming a Azure Sentinel expert
I have been working on Azure Sentinel projects for the past 12 months and writing IP which uses Azure Sentinel, a scalable, cloud-native, security information event management (SIEM) and security orchestration automated response (SOAR) solution.

Recently, while working on a Sentinel project for a major enterprise I became aware of a training that Ofer Shezaf from Microsoft has shared and I highly recommend for those who would like to learn and become an expert on Azure Sentinel to check out the the material and curriculum.
The training program includes 16 modules and includes presentations, relevant product documentation, blog posts, and other resources and if you are already familiar with Sentinel, check out the module 9, my preferred one.
Overview
– Module 1: Technical overview
– Module 2: Azure Sentinel role
Designing Your Deployment
– Module 3: Cloud architecture and multi-workspace/tenant support
– Module 4: Collecting events
– Module 5: Log Management
– Module 6: Integrating threat intelligence
Creating Content
– Module 7: Kusto Query Language (KQL) – the starting point
– Module 8: Writing rules to implement detection
– Module 9: Creating playbooks to implement SOAR
– Module 10: Creating workbooks to implement dashboards and apps
– Module 11: Implementing use cases
Security Operations
– Module 12: A day in a SOC analyst’s life, incident management, and investigation
– Module 13: Hunting
Advanced Topics
– Module 14: Automating and integrating
– Module 15: Roadmap – since it requires an NDA, contact your Microsoft contact for details.
– Module 16: Where to go next?
You can find the training material here
Image sources: Source image: https://docs.microsoft.com/en-us/azure/sentinel/overview
NEW Entitlement Management: Automating employee and partner access requests, approvals and auditing
Microsoft announced today the public preview of the Entitlement Management, which is part of the Azure AD Identity Governance.
I have been working with it since Private Preview, having deployed it ona Proof of Concept for a customer in Australia, for a scenario where user onboarding with workflow approval to access applications is a critical requirement.
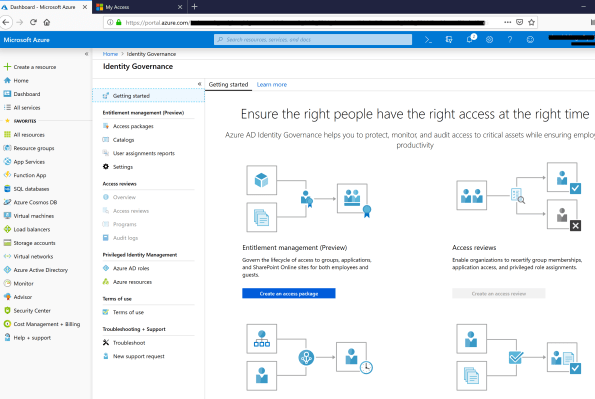
Azure AD entitlement management works with Azure AD B2B to enable collaboration across business partners. Employees from a business partner can request access to resources using the same access packages and our policy engine, including provisioning their accounts upon approval by a business sponsor. This makes it simple to grant access to a specified set of resources for your business partners while knowing your processes are compliant and secure.
Here are some of capabilities of entitlement management:
- Create packages of related resources that users can request
- Define rules for how to request resources and when access expires
- Govern the lifecycle of access for both internal and external users
- Delegate management of resources
- Designate approvers to approve requests
- Create reports to track history
To try these features in your own directory, sign in to the Azure portal as an administrator, and go to the Azure Active Directory > Identity governance section.
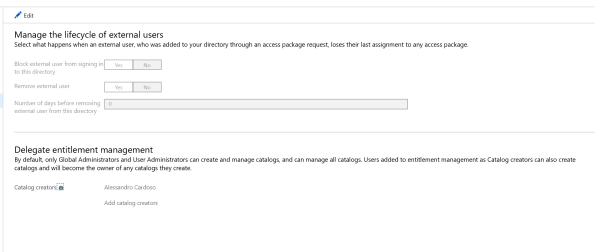
In summary, with the ELM preview, Azure AD now provide:
- Access request workflows, where you can configure different approval workflows for different groups of employees or guests who might request access.
- Time-limited access for groups, apps, and sites, so users who are approved don’t retain access indefinitely—their access can be set to automatically expire.
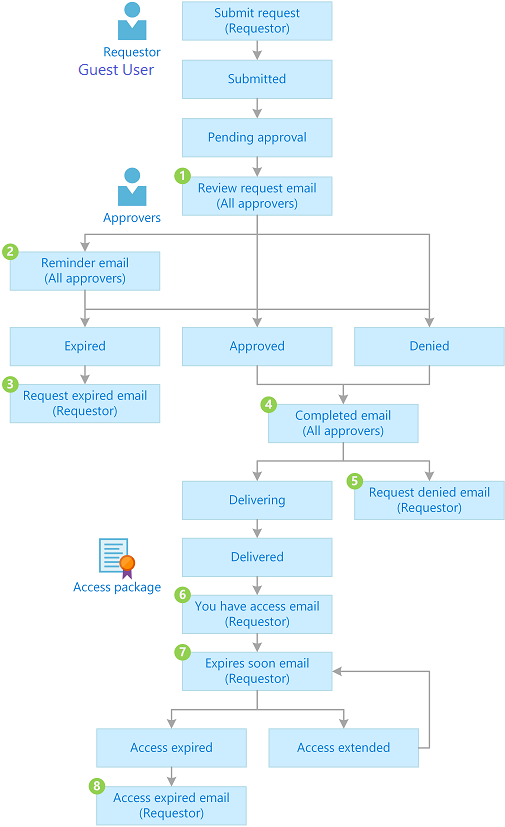
Request Workflow with approval…
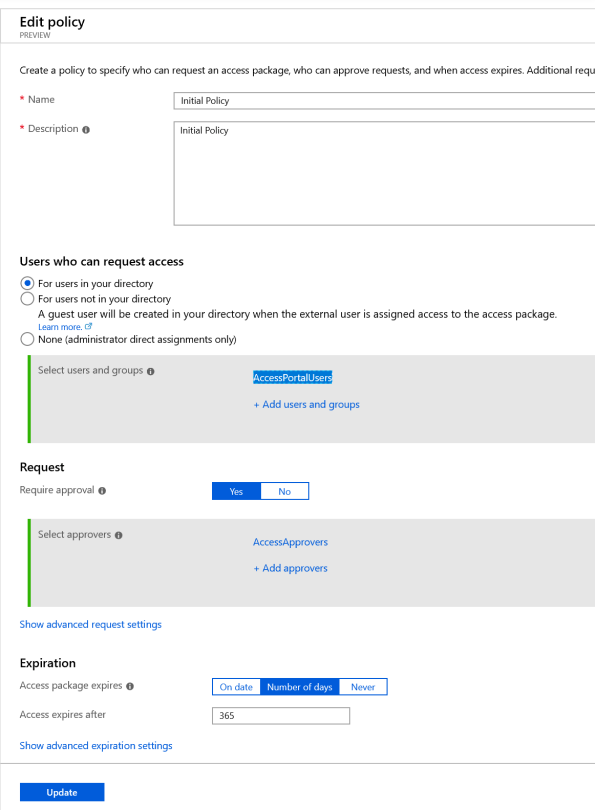
Creating a Policy …
Note: Entitlement management reaquires Azure AD Premium P2 or Enterprise Mobility + Security (EMS) E5.
For an overview of Identity Governance and entitlement management, watch the following video from the Ignite 2018 conference: https://youtu.be/aY7A0Br8u5M
For more information see https://docs.microsoft.com/en-au/azure/active-directory/governance/entitlement-management-overview
Our new SIEM tool: Microsoft Azure Sentinel, intelligent security analytics for your entire enterprise
As we know, many legitimate threats go unnoticed and with the unsurprising high volume of alerts and your team spending far too much time in infrastructure setup or BAU tasks, you need a solution that empowers your existing SecOps team to see the threats clearer and eliminate the distractions.

That’s why we reimagined the SIEM tool as a new cloud-native solution called Microsoft Azure Sentinel. Azure Sentinel provides intelligent security analytics at cloud scale for your entire enterprise. Azure Sentinel makes it easy to collect security data across your entire hybrid organization from devices, to users, to apps, to servers on any cloud.
Collect data across your enterprise easily – With Azure Sentinel you can aggregate all security data with built-in connectors, native integration of Microsoft signals, and support for industry standard log formats like common event format and syslog.
Analyze and detect threats quickly with AI on your side – Security analysts face a huge burden from triaging as they sift through a sea of alerts, and correlate alerts from different products manually or using a traditional correlation engine.
Investigate and hunt for suspicious activities – Graphical and AI-based investigation will reduce the time it takes to understand the full scope of an attack and its impact. You can visualize the attack and take quick actions in the same dashboard.
Automate common tasks and threat response – While AI sharpens your focus on finding problems, once you have solved the problem you don’t want to keep finding the same problems over and over – rather you want to automate response to these issues.
More Information:
https://azure.microsoft.com/en-us/services/azure-sentinel/#documentation
Azure Sentinel preview is free
There will be no charges specific to Azure Sentinel during the preview. Pricing for Azure Sentinel will be announced in the future and a notice will be provided prior to the end of the preview. Should you choose to continue using Azure Sentinel after the notice period, you will be billed at the applicable rates
Password-less VM – The importance of securing your IaaS Linux VM in the Public Cloud
When creating a VM in the Public Cloud, some would think that the Provider would be responsible for its security. Guess what, you are responsible for its security.
A common misunderstanding is assuming that a strong password would do the job of securing the VM access. To prove that is not good enough, yesterday I created a VM in Azure for a Containers Lab work and in less than 9hrs, I had 8712 failed login attempts as it shows in the picture above.

Creating a more Secure VM
So, what should you do to protect the access to my public VM?
“Password-less VM”: Using SSH public key, instead of password, will greatly increase the difficulty of brute-force guessing attack.
A “password-less” VM includes:
- A username that is not standard such as “root” or “admin”: Azure already help you with that, by not allowing you to create “root” or “admin” as a username. Also note that in Linux, the username is case sensitive.
- No password for the user; no password-based login permitted. Instead, configure Private key/certificate SSH authentication: That’s a must!
- A randomized public SSH port.

Verifying
Using the below Linux command line, you should see a line showing: PasswordAuthentication no
$ sudo tail -n 10 sshd_config
Detailed Steps
Check out the Quick steps: Create and use an SSH public-private key pair for Linux VMs in Azure article on how to configure those steps.
What else should you do?
Azure offers great protection options for Azure VM’s. It’s definitely a must that you:
- Install Microsoft Monitoring Agent to enable Azure Security Center which will help you prevent, detect, and respond to threats. Security Center analyzes the security state of your Azure resources. When Security Center identifies potential security vulnerabilities, it creates recommendations. The recommendations guide you through the process of configuring the needed controls. For detailed information see https://docs.microsoft.com/en-us/azure/security-center/quick-onboard-linux-computer
- Configure Security Policies, which drives the security recommendations you get in Azure Security Center.
- Configure Just-in-time (JIT) virtual machine (VM) access which can be used to lock down inbound traffic to your Azure VMs, reducing exposure to attacks while providing easy access to connect to VMs when needed. Configure custom ports and customize the following settings:
Protocol type– The protocol that is allowed on this port when a
request is approved.
Allowed source IP addresses- The IP ranges that are allowed on this port when a request is approved.
Maximum request time– The maximum time window during which a specific port can be opened.
- Configure Network security groups and rules to control traffic to virtual machines
- Configure dedicated network connection between your on-premises network and your Azure vNets, either through a VPN or through Azure ExpressRoute: Production services should not be exposing SSH to the internet.
Stay safe!
Article also published in my Linkedin page: https://www.linkedin.com/pulse/password-less-vm-importance-securing-your-iaas-linux-cardoso/?published=t
Remove yourself as guest user of a partner organisation AD tenant

In the past, when working with partner organisations where you were invited to access shared resources or applications, in order to get your access removed/revoked you would need to contact their Global Admin and ask them to remove you. That was not an easy task!
Now, Microsoft released a Azure B2B update which will allow you to remove yourself from the partner organisation AD tenant

When a user leaves an organization, the user account is “soft deleted” in the directory.
By default, the user object moves to the Deleted users area in Azure AD but is not permanently deleted for 30 days. This soft deletion enables the administrator to restore the user account (including groups and permissions), if the user makes a request to restore the account within the 30-day period.

If you permanently delete a user, this action is irrevocable.
These highly-requested capabilities simplify and modernize your collaboration. They also empower your partner users and help you with your GDPR obligations.
You can find more information about this an other new exciting features of Azure B2B at : https://docs.microsoft.com/en-au/azure/active-directory/active-directory-b2b-leave-the-organization
If you’re interested in viewing or deleting personal data, please see the Azure Data Subject Requests for the GDPR article. If you’re looking for general info about GDPR, see the GDPR section of the Service Trust portal.
New Azure B2B Invite process.
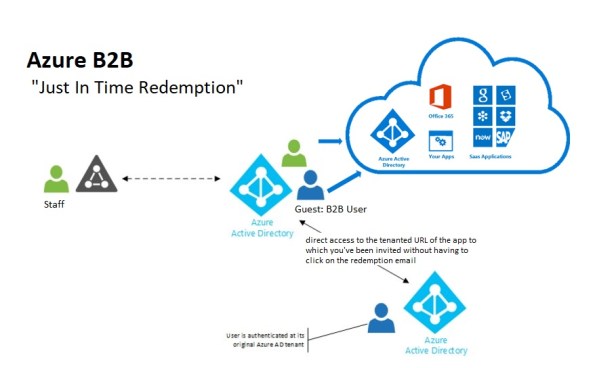 New Azure B2B Invite process: Redemption through a direct link
New Azure B2B Invite process: Redemption through a direct link
“Just in Time Redemption”.
In the past, in order for your guest/partner users to access a shared resources utilising Azure B2B Collaboration, they would have had to be invited by email to access resources/apps on your Azure Tenant. When receiving the email, your guest/partner clicks on the invitation link which will trigger its acceptance and consequent adding the guest/partner account as a guest user in your tenant and the providing access to the resources or apps you have configured.
Now, although that option still available, your guest/partner users can simply access the application you’ve invited them to. How? You can invite a guest/partner user by sending him/her a direct link to a shared app.
NEW Modernized Consent Experience. When a guest/partner user accesses your organization’s resources for the first time, they will interact with a brand new, simple, modernized consent experience.
 Image source:https://cloudblogs.microsoft.com/enterprisemobility/2018/05/14/exciting-improvements-to-the-b2b-collaboration-experience/
Image source:https://cloudblogs.microsoft.com/enterprisemobility/2018/05/14/exciting-improvements-to-the-b2b-collaboration-experience/
After any guest user signs in to access resources in a partner organization for the first time, they see a Review permissions screen.
The guest/partner user must accept the use of their information in accordance to the inviting organization’s privacy policies to continue
Upon consent, the guest/partner users will be redirected to the application shared by you.
How it works:
-
-
- You want your guest/partner user to access a specific application
- You add them as a guest user to your organization (In the Azure Portal, go to Azure Active Directory -> Users -> New Guest User)
-

- In the message invitation, type the link to the application you want them to have access to
- Now, your guest/partner user will only have to click on the link to the application to immediately access it after giving consent.
It’s very simple isn’t it?
Tips to help you take appropriate action to catch illegal activity
Below are some tips to help you take appropriate action to catch illegal activity:
Azure AD reporting API
Use the Azure Active Directory Reporting API’s, which provide programmatic access to the data through a set of REST-based APIs and the data of these reports is very useful to your applications, such as SIEM systems, audit, and business intelligence tools.
Azure AD reporting API can be used to extract data from Azure AD and Azure B2C
Note: You can call these APIs from a variety of programming languages and tools.
For more information on how to use and samples see:
- https://docs.microsoft.com/en-us/azure/active-directory/active-directory-reporting-api-getting-started-azure-portal
- https://docs.microsoft.com/en-us/azure/active-directory/active-directory-reporting-api-audit-samples
Enable Audit Recording for O365
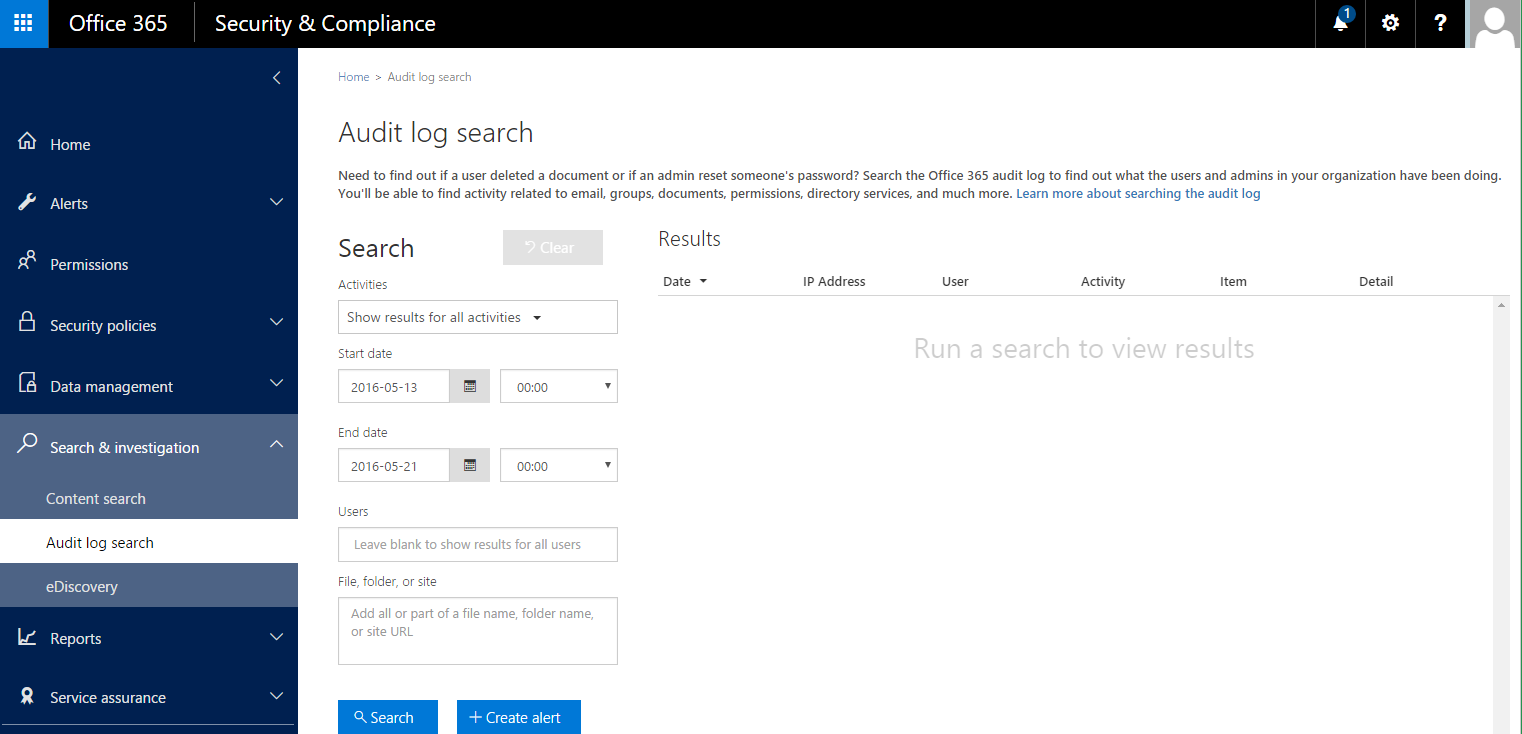
Source: https://blogs.technet.microsoft.com/office365security/finding-illicit-activity-the-old-fashioned-way/
Even the best automated detection systems will fight to catch all illegal activity and they need your help to detect anomalies.
Some audit logging is automatically enabled for you in Office 365; however, mailbox audit logging is not turned on by default
So, if you are a serious about security, Office 365 offers a wide variety of security related reports and data that you can review to manually find illegal activities:
It only takes a few minutes to configure and it will dramatically improve your security posture: To turn it on, just click Start recording user and admin activity on the Audit log search page in the Security & Compliance Center.
Note: If you don’t see this link, auditing has already been turned on for your organization. You only have to do this once.
After you turn it on, a message is displayed that says the audit log is being prepared and that you can run a search in a couple of hours after the preparation is complete.
For more information, follow the instructions here: https://support.office.com/en-us/article/Search-the-audit-log-in-the-Office-365-Security-Compliance-Center-0d4d0f35-390b-4518-800e-0c7ec95e946c?ui=en-US&rs=en-US&ad=US.
After you’ve enabled audit logging you can Search the audit log in the Office 365 Security & Compliance Center to find out who has logged into your user mailboxes, sent messages, and other activities performed by the mailbox owner, a delegated user, or an administrator.
You can Download all results as raw data from the Office 365 audit log to a CSV file.
The table below describe the activities that are audited in Office 365. You can search for these events by searching the audit log in the Security & Compliance Center. Click one of the following links to go to a specific table.
Windows 2016 released and with it Hyper-V and System Center
Microsoft released today at the Microsoft Ignite conference in Atlanta the newest release of Windows Server 2016!
Windows Server 2016 is jam-packed with innovation and customer response has been overwhelming, with more than half a million devices running the final Technical Preview. These customers range from large global enterprises to private cloud hosters to organizations of every size from every corner of the globe – Erin Chapple, General Manager, Windows Server
Windows Server 2016 delivers powerful innovation across three areas:
- Advanced Multi-layer Security: Use Shielded Virtual Machines to help protect your virtual machines from a compromised fabric as well as improve your compliance. Shielded Virtual Machines are encrypted using BitLocker and will run on healthy hosts. To help prevent attacks and detect suspicious activity with new features to control privileged access, protect virtual machines and harden the platform against emerging threats.Watch an introduction to Shielded Virtual Machines
- Software-defined Datacenter with Hyper-V: Run your datacenter with the utmost confidence with an automated, resilient server operating system. Azure utilises Windows Server and Hyper-V at a massive scale. Windows Servers delivers a more flexible and cost-efficient operating system for any datacenter, using software-defined compute, storage and network features inspired by Azure. Explore server virtualization with Hyper-V
- Cloud-ready Application Platform: Run your existing apps on Windows Server 2016 without modifying them. Take advantage of enhanced security and efficiency features in the fabric. Applications are at the heart of every organization and its ability to serve customers and compete effectively for their loyalty. Windows Server 2016 delivers new ways to deploy and run both existing and cloud-native applications – whether on-premises or in Microsoft Azure – using new capabilities such as Windows Server Containers and the lightweight Nano Server deployment option. Learn more about containers and Learn more about Azure Service Fabric on Windows Server 2016
Availability: Windows Server 2016 is available for evaluation starting today
Note: Volume licensing customers will be able to download fully licensed software at General Availability in mid-October.
Shielded VM’s: Virtualization security is a major investment area in Hyper-V 2016
 SECURITY – Protecting the company data should be a priority.
SECURITY – Protecting the company data should be a priority.
Protecting a Virtual Machine(VM) guest from a possible host compromised as well as the certain that on a 3rd party hosting environment your VM will be protected in addition to the protection applied to the hosts is a major investment area in Hyper-V 2016.
If you find that Microsoft is helping you and your business and find it has amazing technologies as I as do, please help me out by recommending it on Recomazing a new tech platform where socially connected networks store and share trusted recommendations. Please click here to help our community.
Taking into consideration that a VM is a file, stored somewhere on a storage on locally in the Hyper-v host, it needs to be protected from attacks to the storage system, the network, while it is backed up or taken or copied to other systems.
To help protect against compromised fabric, Windows Server 2016 Hyper-V introduces Shielded VMs. A Shielded VM, requires a VM to be created as generation 2, which has a virtual TPM, is encrypted using BitLocker and can only run on healthy and approved hosts in the fabric. So, if someone copy either maliciously or accidentally the VM to a non-approved host, the VM (which is encrypted), won’t start and cannot be used to be mounted to allow access to it’s file system.
Shielded VM’s use several features to make it harder for Host administrators and malware on the host to inspect, tamper with, or steal data from the state of a shielded virtual machine. Data and state is encrypted, Hyper-V administrators can’t see the video output and disks, and the virtual machines can be restricted to run only on known, healthy hosts, as determined by a Host Guardian Server.
A configured Shielded VM has:
- BitLocker encrypted disks
- A hardened VM worker process (VMWP) that helps prevent inspection and tampering
- Automatically encrypted live migration traffic as well as encryption of its runtime state file, saved state, checkpoints and even Hyper-V Replica files (from 2016 TP5)
- Blocked console access
- Blocked PowerShell Direct
- Blocked Guest File Copy Integration Components
- Blocked services that provide possible paths from a user or process with administrative privileges to the VM.
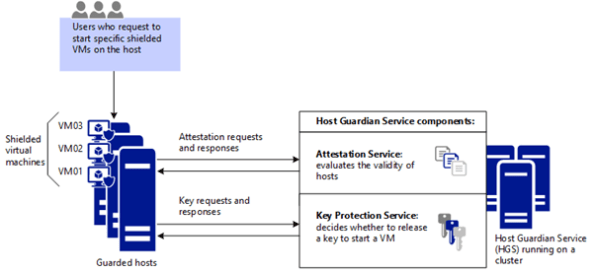
Image Source: Microsoft – https://technet.microsoft.com/en-us/library/mt599611.aspx
With the release of Windows Server 2016 TP5, the Hyper-V team at Microsoft made shielded virtual machines compatible with Hyper-V Replica. As with copying/moving the VM, to replicate a shielded VM, the host you want to replicate to must be authorized to run that shielded VM.
The Host Guardian Service supports two different deployments of a Guarded fabric (attestation modes): TPM-trusted attestation (Hardware based) and Admin-trusted attestation (AD based).
I hope you walk away with a better understanding of the Hyper-V Shielded VM solution from this post.




