Archive
Tips to help you take appropriate action to catch illegal activity
Below are some tips to help you take appropriate action to catch illegal activity:
Azure AD reporting API
Use the Azure Active Directory Reporting API’s, which provide programmatic access to the data through a set of REST-based APIs and the data of these reports is very useful to your applications, such as SIEM systems, audit, and business intelligence tools.
Azure AD reporting API can be used to extract data from Azure AD and Azure B2C
Note: You can call these APIs from a variety of programming languages and tools.
For more information on how to use and samples see:
- https://docs.microsoft.com/en-us/azure/active-directory/active-directory-reporting-api-getting-started-azure-portal
- https://docs.microsoft.com/en-us/azure/active-directory/active-directory-reporting-api-audit-samples
Enable Audit Recording for O365
Source: https://blogs.technet.microsoft.com/office365security/finding-illicit-activity-the-old-fashioned-way/
Even the best automated detection systems will fight to catch all illegal activity and they need your help to detect anomalies.
Some audit logging is automatically enabled for you in Office 365; however, mailbox audit logging is not turned on by default
So, if you are a serious about security, Office 365 offers a wide variety of security related reports and data that you can review to manually find illegal activities:
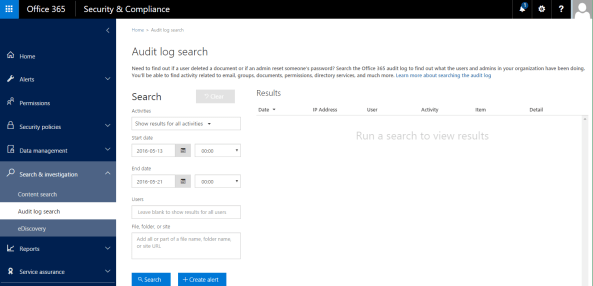
It only takes a few minutes to configure and it will dramatically improve your security posture: To turn it on, just click Start recording user and admin activity on the Audit log search page in the Security & Compliance Center.
Note: If you don’t see this link, auditing has already been turned on for your organization. You only have to do this once.
After you turn it on, a message is displayed that says the audit log is being prepared and that you can run a search in a couple of hours after the preparation is complete.
For more information, follow the instructions here: https://support.office.com/en-us/article/Search-the-audit-log-in-the-Office-365-Security-Compliance-Center-0d4d0f35-390b-4518-800e-0c7ec95e946c?ui=en-US&rs=en-US&ad=US.
After you’ve enabled audit logging you can Search the audit log in the Office 365 Security & Compliance Center to find out who has logged into your user mailboxes, sent messages, and other activities performed by the mailbox owner, a delegated user, or an administrator.
You can Download all results as raw data from the Office 365 audit log to a CSV file.
The table below describe the activities that are audited in Office 365. You can search for these events by searching the audit log in the Security & Compliance Center. Click one of the following links to go to a specific table.
Do you have questions on Containers? #AskBenArmstrong
Fundamentally, Containers are an isolated, resource controlled, and portable runtime environment which runs on a host machine or virtual machine and allows you to run an application or process which is packaged with all the required dependencies and configuration files on its own.
When you containerize an application, only the components needed to run this application and of course the application itself are combined into an image, which are used to create the Containers.
How are you utilising containers? Do you have questions on Containers? On Tuesday, 24th April, Microsoft Program Manager Ben Armstrong, will be answering your questions on Containers. It is a rare opportunity. Don’t miss out.
- Date and Time: Tuesday, Apr 24, 2018, 4pm CEST (7am PDT / 10am EDT) Duration: Approx. 1 hour
- Date and Time: Tuesday, Apr 24, 2018, 10am PDT / 1pm EDT (7pm CEST) Duration: Approx. 1 hour
You can also ask questions through twitter until Tuesday by including #AskBenArmstrong.




