Archive
Short list of Microsoft Desktop Virtualisation solutions
And how you can use them in your organization:
VDI: Enables users to access their personalized Windows desktops hosted on servers. For many organizations, virtualizing desktops within the datacenter is seen as an excellent means to provide a centrally-managed Windows desktop to connected users. http://www.microsoft.com/downloads/details.aspx?displaylang=en&FamilyID=8d454921-72d6-45b4-b6ba-ac1c26d337bd
Session Virtualization: Makes it possible for you to run an application or an entire desktop in one location, but have it be controlled in another. Session virtualization allows you to install and manage session-based desktops and applications, or virtual-machine based desktops on centralized servers in the datacenter; deliver images to users, and send keystrokes and mouse movements from user client machines, in turn, back to the server. From a user perspective, applications are integrated seamlessly—looking, feeling, and behaving like local applications. http://technet.microsoft.com/library/cc742806.aspx
MED-V: Provides you with the ability to deploy and manage virtual Windows desktops to help enterprises upgrade to the latest version of Windows, without having to worry about application compatibility. MED-V provides organizations the ability to run two operating systems on one device, adding virtual image delivery, policy-based provisioning, and centralized management. http://technet.microsoft.com/library/ff433588.aspx
App-V: Helps you make business applications available to end users on any authorized PC. App-V decouples applications from the OS and helps to eliminate application-to-application incompatibility, as applications are no longer installed on the local client machine. In addition, application streaming expedites the application delivery process so that your IT department no longer needs to install applications locally on every machine. http://technet.microsoft.com/library/ee958103.aspx
RemoteApp: Enables programs that are accessed remotely through Terminal Services to appear as if they are running on the end user’s local computer. Users can run RemoteApp programs side by side with their local programs. A user can minimize, maximize, and resize the program window, and can easily start multiple programs at the same time. If a user is running more than one RemoteApp program on the same terminal server, the RemoteApp programs will share the same Terminal Services session. http://technet.microsoft.com/library/cc755055.aspx
Data and User Settings: Utilizes folder redirection and roaming profiles to enable you to make the user’s personal profile and data available dynamically on any authorized PC, and to back up personal profiles and data to the datacenter. http://technet.microsoft.com/library/cc732275.aspx
To find more about, visit : http://technet.microsoft.com/en-us/windows/gg276319.aspx?ITPID=insider
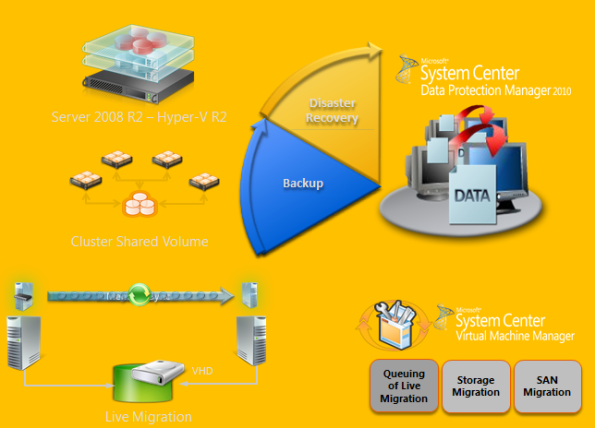
Hyper-V CSV protection with DPM 2010
DPM design for Hyper-V :
- Incremental Backups Only – full only once
- No More Backup Window – online backups
- Application consistency via VSS
- Protect Live Migration VMs in CSV clusters
- Protect whole VM, recover individual items
- Auto Protection of new VMs
- Routine backups – nightly or more frequently
Strategy to Deply DPM 2010 in Hyper-V/CSV environment :
1. Plan:
- Identify Project Requirements and scope
- Simulate using Hyper-V Calculator
- Review Hyper-V design guidelines & Best Practices
- Acquire VSS Hardware Provider & check environment with SDPM SAN Testing Tool:
- Verify that the SAN supports hardware snapshots & is certified for DPM.
- http://blogs.technet.com/dpm/archive/2010/02/05/tested-hardware-vss-provider-table.aspx
- Install the VSS hardware provider
- Self Certifying your SAN. If your SAN is not in the certified list & you have a SAN, run the SCDPM SAN Testing Tool : StartCSVTests.cmd /run ( to be realeased yet )
- Validate a Pilot Environment
- Ready for Deployment
- Integration components should be updated on both VMs.
- Ensure that Live Migration is functional
2. Deploy : Protected CSV server
- Install all recommended prerequisites:
| General Prerequisite | Install the integration components on the guests. For more information, see Install a Guest Operating System (http://go.microsoft.com/fwlink/?LinkId=165041). |
| Microsoft Windows Server 2008 SP2 | Install Microsoft Windows Server 2008 SP2 OR Install the Microsoft Hyper-V prerequisites (http://go.microsoft.com/fwlink/?LinkID=133781). |
| Microsoft Windows Server 2008 R2 | Install the following on the host computer:KB975354 (http://support.microsoft.com/kb/975354)KB975921 (http://support.microsoft.com/kb/975921) |
- Failover Cluster Validation
- Enable Automount : Enable Auto mount on the host for successful child partition backups : MOUNTVOL /E
- Install Hardware Provider:Ensure that VSS hardware providers are installed : vssadmin list providers
- Validate Hardware snapshots
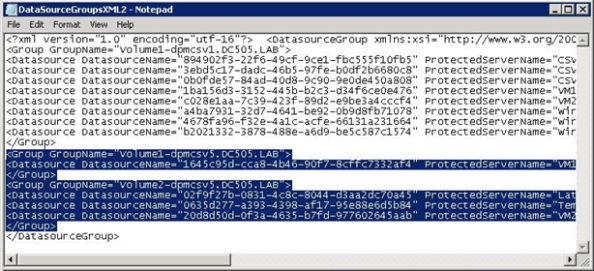
- Use DSConfig Tool to serialize backups (for software snapshots providers only) :
· Problem:With software snapshots, simultaneous triggering of VM backups (especially scale deployments) will cause backup jobs to time out and fail.
· Enable Per CSV LUN Serialization:This serialization limits the number of virtual machine backups happening on a single CSV LUN.Create a DataSourceGroups.xml file by running the DSConfig.ps1 script on any one node of a cluster containing CSV.Place the file in the DPM server at %PROGRAMFILES%\Microsoft DPM\DPM\Config.Repeat step 1 for every cluster that is protected by a DPM server.The DataSourceGroups.xml file needs to be updated only when virtual machines are added, deleted, or modified in the cluster and protection is configured for them.
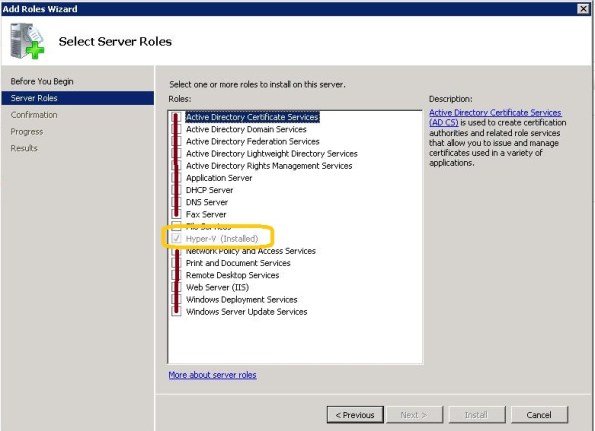
3. Deploy : DPM 2010 server
- Enable Hyper-V Role on DPM Server :DPM supports item-level recovery (ILR), which allows you to do granular recovery of files, folders, volumes, and virtual hard disks (VHDs) from a host-level backup of Hyper-V virtual machines to a network share or a volume on a DPM protected server. You must have the Hyper-V role enabled on the DPM server to perform item-level recoveries. During item-level recovery, DPM has to mount the VHDs of the protected virtual machines
- Install DPM server pre-requisites
- Install DPM 2010
- Turn off “TCP Chimney offload”For better throughput, TCP Chimney Offload should be turned off.
- Allocate Storage Pool & Deploy Agents
- Datasourcegroups.xml file:
- Merge the DatasourceGroups.XML file for all CSVs protected by DPM server. This is applicable when software providers are used on the CSV cluster.
- Copy the <Group> tags from all the DataSourceGroup.xml files generated and add the text between the <DataSourceGroup> tags. The DataSourceGroups.xml file will now contain one <header> tag, one <DataSourceGroup> tag, and <Group> tags from all CSV clusters.
- Configure Protection Groups
- DPM2010 provides Datasource caching for faster enquiry.
- Remember to clear cache if new VMs have been added
- Enable AutoProtection:
Script to Auto-add VMs : http://blogs.technet.com/dpm/archive/2009/12/03/hyper-v-protection-with-dpm-2010-beta-how-to-automatically-protect-new-virtual-machines.aspx
TechNet Radio: TechNet on: Virtualization Best Practices
About this Video : http://technet.microsoft.com/en-us/edge/technet-radio-technet-on-virtualization-best-practices.aspx
Join Keith Combs and Matt Hester as they discuss virtualization best practices with Microsoft Director, Edwin Yuen. Edwin was part of the System Center Virtual Machine Manager (SCVMM) team for several years and has talked with thousands of customers about their virtualization problems and solutions. Expect a lively discussion on Hyper-V, SCVMM, SANS, Clustering and other technologies used to create world class virtualization solutions.
Project Phoenix : MSDN Ultimate subscriptions to give away
Hi Everyone,
fellow MVPs Greg Low, Darren Gosbell , Arnie Rowland and Rod Colledge are giving away 7 MSDN Ultimate subscriptions.
Called Project Phoenix, it awards (among other things) Microsoft Visual Studio Ultimate with MSDN subscription to unemployed or underemployed developers who commit to developing a project using Microsoft tools for an eligible non-profit organisation. More details on the program can be found here.
Project Criteria;
- Client is an Australian or New Zealand non-profit, school or church,
- Solves a problem or satisfies a need for the client,
- Client desires the project and is supportive,
- Uses any combination of .NET 4.0, Windows Server 2008, SQL Server 2008, or Windows Phone 7,
- May be a new software solution, or an upgrade to an existing software solution,
- Additional consideration given projects that will be posted on Codeplex with a GPL license
An eligible developer may submit project proposal information here.
An eligible non-profit may submit a project proposal here. Eligible developers without a project proposal may select from one of the available projects listed below;
Hyper-V : Virus scanning recommendations : exclusions
To protect your Hyper-V Host, we recommend that you install the antivirus software within the Host and also within virtual machine.
It also, may be necessary to configure the real-time scanning component within the antivirus software to exclude files and entire folders :
Configure the real-time scanning component within your antivirus software to exclude the following directories and files:
- Default virtual machine configuration directory (C:\ProgramData\Microsoft\Windows\Hyper-V)
- Custom virtual machine configuration directories Default virtual hard disk drive directory (C:\Users\Public\Documents\Hyper-V\Virtual Hard Disks)
- Custom virtual hard disk drive directories Snapshot directories Vmms.exe
- (Note: May need to be configured as process exclusions within the antivirus software)
- Vmwp.exe (Note: May need to be configured as process exclusions within the antivirus software)
Additionally, when you use Live Migration together with Cluster Shared Volumes on Windows Server 2008 R2, exclude the CSV path “C:\Clusterstorage” and all its subdirectories
Also exclude the root directory that contain your Virtual machines and configuration files
Also exclude the following files extensions :
VHD, VSV, ISO, AVHD, VFD, and XML,
Hyper-V : 4 Tips to improves overall performance
Here are some performance tips that will improve the Hyper-V experience:
1. Allways install the the Integration Services. This will dramatically improves overall workload performance. ( Note : the Hyper-V Integration Services are already installed as part of W2008 R2 )
Note : it is important to check for the Virtual Machine Bus in Device Manager, to look for device malfunction.
2. DO NOT RUN services on the parent partition other the Hyper-V. ( This is suppose to be obvious!! )
Run them in virtual machines instead The parent is differentiated for scheduling.
3. When possible, use Windows Server 2008 and newer as the guest OS – fully enlightened. Enlightenments reduce the cost of OS functions like memory management
Keep in mind that new operating systems run better than old operating systems.
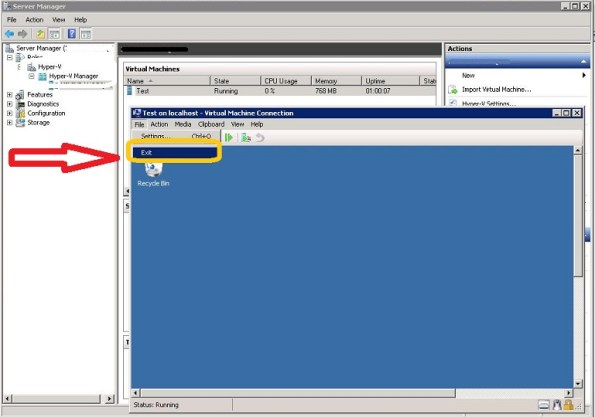
4. Hyper-V Manager and Virtual Machine Connection sessions should be closed after use. It consume resources. Hyper-V manager causes WMI activity in parent partition. Also, video emulation is disabled when Virtual Machine Connection is closed.