Archive
Oracle running on Azure
Yes, your heard right
Oracle virtual machines on Windows Azure are now in preview, Multi-Factor Authentication is generally available and we have an announcement regarding SQL Database.
Microsoft and Oracle provide end-to-end support for customers running business-critical Oracle software on Windows Azure
Oracle, Oracle WebLogic Server, and the Java development environment are now available, in preview, in the Windows Azure Virtual Machines Image Gallery. These images include licenses for the Oracle software that they contain.
During the preview period, there is no charge for the included Oracle licenses. You will pay only for the Windows Azure compute and storage resources that your Virtual Machine consumes. If you would prefer to use an Oracle software license that you already own, you can do that too. Just choose a Windows Server image from the Image Gallery and install the Oracle software yourself.
Whether you bring your own Oracle license or use one of the license-included images, you now have increased flexibility and choice in where to deploy your applications and the peace of mind that comes from knowing you will be fully supported by Oracle.
To get started, sign in to the Windows Azure Management Portal and add a new Virtual Machine from the Image Gallery.
For more information, visit the Oracle information page on the Windows Azure website.
System Center 2012 SP1 : Public beta available. What’s new in SCVMM?
System Center 2012 SP1 beta has just been public released
Here is what is new in System Center Virtual Machine 2012 SP1
Windows Server 2012 and SQL Server 2012 Support
With this Beta release, all System Center 2012 SP1 components are now enabled to manage and run in a Windows Server 2012 environment. System Center 2012 SP1 also now supports the use of SQL Server 2012.
Network Virtualization
With System Center 2012 SP1 you can take advantage of the Virtual Machine Manager’s ability to manage Hyper-V network virtualization across multiple hosts, simplifying the creation of entire virtual networks.
Plus,
- Extend the VMM console with Add-ins
- Support for Windows Standards-Based Storage Management Service, thin provisioning of logical units and discovery of SAS storage
- Ability to convert VHD to VHDX, use VHDX as base Operating System image
- Support for vSphere 5.0 and Citrix XenServer 6.0
- Performance enhancement
And much more!…But to know it you will need to download and install it to find out 🙂 and keep me updated on what you find out!
Begin your evaluation of System Center 2012 SP1 with Windows Server 2012 today:
- Download the Beta
- Visit the TechNet System Center 2012 SP1 Beta library for technical documentation to support your evaluation
Infrastructure Planning and Design Guide for VMM 2012
The new IPD Guide for System Center 2012 – Virtual Machine Manager is now available to download
Infrastructure Planning and Design streamlines the planning process by:
- Defining the technical decision flow through the planning process.
- Listing the decisions to be made and the commonly available options and considerations.
- Relating the decisions and options to the business in terms of cost, complexity, and other characteristics.
- Framing decisions in terms of additional questions to the business to ensure a comprehensive alignment with the appropriate business landscape
Download the guide now: http://go.microsoft.com/fwlink/?LinkId=245473
Windows 2012 Hyper-V Replica : Deployment Scenarios, Functionality and Step by Step by using SSL Certificate Part I
With Windows 2012 around the corner ( first week of august 2012 ), you probably started planning the deployment already.
I am starting a series of blog posting with step by steps. The first one is about Hyper-V Replica, a real nice feature.
Hyper-V Replica. what is ?
Hyper-V replica is a new feature of Windows 2012 that enables you to replicate any Virtual Machine (yes, copy the entire VM: VHD/VHDX and configuration ) from one Hyper-V Server to another, without storage or any special hardware. You only need 2 servers running Windows 2012 Hyper-V.
You can replicate the content over the LAN or WAN (without compromising the link) by using HTTP or HTTPS protocols using SSL certificates inclusive.
Once you enable the Hyper-V Replica on the VM, the source host starts to maintain a HRL (Hyper-V Replica Log file) for the VHDs. Every 1 write by the VM = 1 write to VHD and 1 write to the HRL. Depending on bandwidth availability, the logfiles are sent to the target host every 5 minutes(setting not configurable). On the target the Hyper-V Replica mechanism run asynchronous, processing the log file in reverse order, allowing it only to store the latest writes. It replicates only the changes.
Note: After 5 minutes, if the replay hasn’t happened then you get an alert. The replica log file replication will take up to 30min to complete before going into a failed state where your intervention will be required to look at the issue and fix it.
The configurations at each site do not have to be the same with respect to server or storage hardware. Hyper-V Replica provides the option to restore virtualized workloads to a point in time depending on the Recovery History selections for the virtual machine.
Really easy to deploy and use.
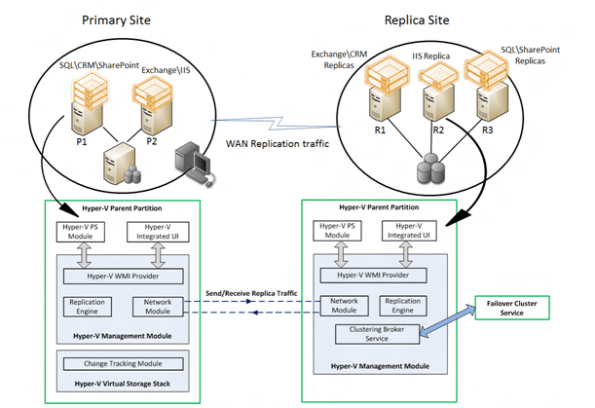
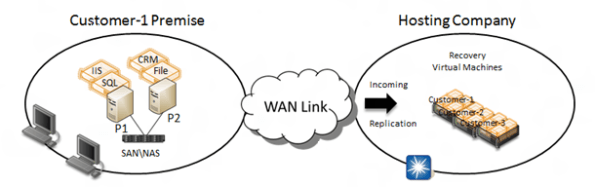
Deployment Scenarios:
– Between 2 sites (DataCenter replication to small offices)
– Cross premises DR solution
Cluster
Hyper-V Replica works with clusters. In fact you can do the following replications:
- Standalone host to cluster
- Cluster to cluster
- Cluster to standalone host
NOTE : Hyper-V Replica is NOT an alternative to clustering. It is not intended for High Availability purposes.
Functional description
• Replication Engine: Manages the replication configuration details and handles initial replication, delta replication, failover, and test-failover operations. It also tracks virtual machine and storage mobility events and takes appropriate actions as needed (i.e. it pauses replication events until migration events complete and then resumes where they left off).
• Change Tracking: Provides a virtual machine level change tracking mechanism on the primary server by keeping track of the write-operations, which happen in the virtual machine.
• Network Module: The Networking Module provides a secure and efficient compressed network channel to transfer virtual machine replicas between Primary and Replica site.
• Hyper-V Replica Broker role: The Hyper-V Replica Broker role is configured in a Windows Server 2012 Failover Cluster. This functionality supports seamless replication even in the event of a migration of a replica virtual machine from one cluster node to another.
• Management Experience: Hyper-V Manager UI; Failover Cluster Manager UI; PowerShell scripting; Hyper-V Replica APIs.
Step by Step – Part I
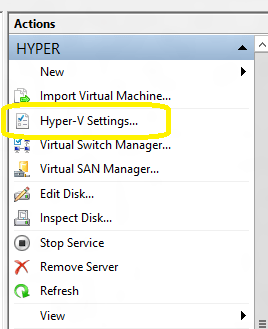
On the source Hyper-V Server
1. Open the Hyper-V Server Manager and click on the Hyper-V server. Then in the right pane, click on Hyper-V settings
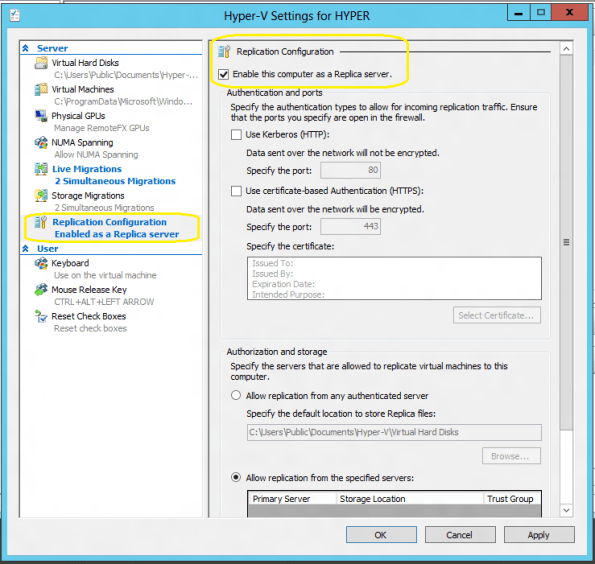
2. On the Hyper-V settings page, click on Replication Configuration on the left pane
3. On the Replication Configuration, click on Enable this computer as a Replica Server
4.You have now the choose how the replication will occur : by using HTc.TP (port 80) or HTTPS (port 443, with encryption).
HTTPS: If you select HTTPS, I recommend you to buy an SSL Certificate from a trusted Certification Authority (CA), then :
a. Create an INF file for an Wildcard certificate request. Use the following example and replace the subject with the hyper-v servers domain name. Save the content in a text file as cert.inf for example.
[Version]
Signature=”$Windows NT$”
[NewRequest]
Subject = “CN=*.YOURDOMAIN.local”
Exportable = TRUE ; Private key is exportable
KeyLength = 2048 ; Common key sizes: 512, 1024, 2048, 4096, 8192, 16384
KeySpec = 1 ; AT_KEYEXCHANGE
KeyUsage = 0xA0 ; Digital Signature, Key Encipherment
MachineKeySet = True ; The key belongs to the local computer account
ProviderName = “Microsoft RSA SChannel Cryptographic Provider”
ProviderType = 12
RequestType = CMC[EnhancedKeyUsageExtension]
OID=1.3.6.1.5.5.7.3.1 ;Server Authentication
OID=1.3.6.1.5.5.7.3.2 ;Client Authentication
b. Create a request. Open the command prompt with Administrative rights ( run as Administrator ) and type the following:
certreq –new CERT.inf CERT.req
c. Create the CSR to submit the certificate request to an external CA
certutil -encode CERT.req CERT.csr
d.Upload the ENTIRE content of the text file CERT.csr into the external CA webpage. (could be any external trusted CA)
e.After the certificate is issued and you received the email with the certificate, open the command prompt and type the following commands to import and store the certificate on all Hyper-V servers ( source and target )
certreq -accept CERT.cer
certutil –store my
HTTP: Select : Use Kerberos HTTP
5. Configure the Authorization and storage. This includes designating a specific location to store replica virtual machine files if the default location is not to be used. Should you not desire to allow all Primary servers to be serviced, there is an option to allow only specific servers (Primary servers) to send replication requests.
If you want to allow all servers within the domain, a wildcard character can be used (e.g. *.yourdomain.local). When using a wildcard, only one storage location can be specified. If individual server entries are used, different storage locations for replica files can be configured. Complete all entries for the Primary Server, Storage Locations, and Security Tag information.
6. Click Apply or OK when finished.
Next article : configuring the target server
SCVMM 2012 : Ports commnications for Firewall Configuration
When you install the SCVMM 2012 you can assign some of the ports that it will use for communications and file transfers between the VMM components.
Note: Not all of the ports can be changed through VMM.
The default settings for the ports are listed in the following table:
| Connection type | Protocol | Default port | Where to change port setting |
| SFTP file transfer from VMware ESX Server 3.0 and VMware ESX Server 3.5 hosts | SFTP | 22 | |
| VMM management server to P2V source agent (control channel) | DCOM | 135 | |
| VMM management server to Load Balancer | HTTP/HTTPS | 80/443 | Load balancer configuration provider |
| VMM management server to WSUS server (data channel) | HTTP/HTTPS | 80/8530 (non-SSL), 443/8531 (with SSL) |
These ports are the IIS port binding with WSUS. They cannot be changed from VMM. |
| VMM management server to WSUS server (control channel) | HTTP/HTTPS | 80/8530 (non-SSL), 443/8531 (with SSL) | These ports are the IIS port binding with WSUS. They cannot be changed from VMM. |
| BITS port for VMM transfers (data channel) | BITS | 443 | During VMM setup |
| VMM library server to hosts file transfer | BITS | 443 (Maximum value: 32768) | During VMM setup |
| VMM host-to-host file transfer | BITS | 443 (Maximum value: 32768) |
|
| VMM Self-Service Portal to VMM Self-Service Portal web server | HTTPS | 443 | During VMM setup |
| VMware Web Services communication | HTTPS | 443 | VMM console |
| SFTP file transfer from VMM management server to VMware ESX Server 3i hosts | HTTPS | 443 | |
| OOB Connection – SMASH over WS-Man | HTTPS | 443 | On BMC |
| VMM management server to in-guest agent (VMM to virtual machine data channel) | HTTPS (using BITS) |
443 | |
| VMM management server to VMM agent on Windows Server–based host (data channel for file transfers) | HTTPS (using BITS) |
443 (Maximum value: 32768) |
|
| OOB Connection IPMI | IPMI | 623 | On BMC |
| VMM management server to remote Microsoft SQL Server database | TDS | 1433 | |
| Console connections (RDP) to virtual machines through Hyper-V hosts (VMConnect) | RDP | 2179 | VMM console |
| VMM management server to Citrix XenServer host (customization data channel) | iSCSI | 3260 | On XenServer in transfer VM |
| Remote Desktop to virtual machines | RDP | 3389 | On the virtual machine |
| VMM management server to VMM agent on Windows Server–based host (control channel) | WS-Management | 5985 | During VMM setup |
| VMM management server to in-guest agent (VMM to virtual machine control channel) | WS-Management | 5985 | |
| VMM management server to VMM agent on Windows Server–based host (control channel – SSL) | WS-Management | 5986 | |
| VMM management server to XenServer host (control channel) | HTTPS | 5989 | On XenServer host in: /opt/cimserver/cimserver_planned.conf |
| VMM console to VMM management server | WCF | 8100 | During VMM setup |
| VMM Self-Service Portal web server to VMM management server | WCF | 8100 | During VMM setup |
| VMM console to VMM management server (HTTPS) | WCF | 8101 | During VMM setup |
| Windows PE agent to VMM management server (control channel) | WCF | 8101 | During VMM setup |
| VMM console to VMM management server (NET.TCP) | WCF | 8102 | During VMM setup |
| WDS provider to VMM management server | WCF | 8102 | During VMM setup |
| VMM console to VMM management server (HTTP) | WCF | 8103 | During VMM setup |
| Windows PE agent to VMM management server (time sync) | WCF | 8103 | During VMM setup |
| VMM management server to Storage Management Service | WMI | Local call |
|
| VMM management server to Cluster PowerShell interface | PowerShell | n/a | |
| Storage Management Service to SMI-S Provider | CIM-XML | Provider-specific port |
|
| VMM management server to P2V source agent (data channel) | BITS | User-Defined | P2V cmdlet option |
Simplify your cloud migration planning with MAP 6.0
The latest release from the Microsoft Assessment and Planning (MAP) team provides organizations with tools to simplify public and private cloud migration planning.
Download the MAP Toolkit 6.0:http://www.microsoft.com/map
New features and benefits from MAP 6.0 release help you:
· Analyze your portfolio of applications for a move to the Windows Azure Platform
· Accelerate private cloud planning with Hyper-V Cloud Fast Track onboarding
· Identify migration opportunities with enhanced heterogeneous server environment inventory
· Assess your client environment for Office 365 readiness
· Determine readiness for migration to Windows Internet Explorer 9
· Discover Oracle database schemas for migration to SQL Server
Hyper-V : Network Design, Configuration and Prioritization : Guidance
There is a lot of posts regarding Hyper-V and network, but I found a lot people still don’t get it.
1. Network Design. How many nic’s we need for production environment for High Availiability:
- 1 for Management. Microsoft recommends a dedicated network adapter for Hyper-V server management.
- 2 ( Teamed ) for Virtual machines.Virtual network configurations of the external type require a minimum of one network adapter.
- 2 ( MPIO ) for SCSI.Microsoft recommends that IP storage communication have a dedicated network, so one adapter is required and two or more are necessary to support multipathing.
- 1 for Failover cluster.Windows® failover cluster requires a private network.
- 1 for Live migration.This new Hyper-V R2 feature supports the migration of running virtual machines between Hyper-V servers. Microsoft recommends configuring a dedicated physical network adapter for live migration traffic. This network should be separate from the network for private communication between the cluster nodes, from the network for the virtual machine, and from the network for storage
- 1 for CSV. Microsoft recommends a dedicated network to support the communications traffic created by this new Hyper-V R2 feature. In the network adapter properties, Client for Microsoft Networks and File and Printer Sharing for Microsoft Networks must be enabled to support SMB
But how about production environments when the blades have only 4 Physical NIC’s?
Option 1. If your vendor does support NPAR technology(Broadcom, QLogic), you will be able to create up to 4 “Virtual Logical NIC’s” per physical NIC ( VLAN/QoS ). Although this solution is not supported by MS, it’s the best solution in terms of performance and it is supported by the vendors. This solution will provide you 100% HA as you can have up to 16 Logical NIC’s.
Option 2. Supported by MS. Allocate 2(two) NIC’sfor the iSCSI using MPIO and then :
| Host configuration | Virtual machine access | Management | Cluster and Cluster Shared Volumes | Live migration | Comments |
| 2 network adapters with 10 Gbps | Virtual network adapter 1 | Virtual network adapter 1 with bandwidth capped at 1% | Network adapter 2 | Network adapter 2 with bandwidth capped at 50% | Supported |
Note that the QoS configuration is based on “per port” and Windows only allows you to cap specify caps – not reserves. This solution, although supported by MS, dos not give you 100% HA.
2. Network Configuration. What need to be enabled/disabled?
| Usage | Number of Network Cards | Comments |
| Management Network(Parent Partition) | 1 Network Card |
|
| Storage ISCSI | 2 Network Cards – Not Teamed |
|
| VM Network (Parent Partition) |
2 Network cards : 1 for Dynamic IP’s 1 for Reserved IP’s |
|
| Cluster Heartbeat | 1 Network Card |
|
| Cluster Shared Volume (CSV) | 1 Network Card |
|
| Live Migration | 1 Network Card |
|
2. Network Prioritization. What need to be enabled/disabled?
By default, all internal cluster network have a metric value starting at 1000 and incrementing by 100. The first internal network which the cluster sees when it first comes online has a metric of 1000, the second has a metric of 1100, etc.
When you create CSV’s, the failover cluster automatically chooses the network that appears to be the best for CSV communication. The lowest Metric value designates the network for Cluster and CSV traffic. The second lowest value designates the network for live migration. Additional networks with a metric below 10000 will be used as backup networks if the “Cluster & CSV Traffic” or “Live Migration Traffic” networks fail. The lowest network with a value of at least 10000 will be used for “Public Traffic”. Consider giving the highest possible values to the networks which you do not want any cluster or public traffic to go through, such as for “ISCSI Traffic”, so that they are never used, or only used when no other networks at all are available.
To view the networks, their metric values, and if they were automatically or manually configured, run the clustering PowerShell cmdlet:
PS > Get-ClusterNetwork | ft Name, Metric, AutoMetric
To change the value of a network metric, run:
PS >Get-ClusterNetwork “Live Migration” ).Metric =800
If you want the cluster to start automatically assigning the Metric setting again for the network named “Live Migration”:
PS > Get-ClusterNetwork “Live Migration” ).AutoMetric = $true
How to override Network Prioritization Behavior?
Option 1. Change the network’s properties. If you select “Do not allow cluster network communication on this network”, then it will not be possible to send any “Cluster & CSV Traffic” or “Live Migration Traffic” through this network, even if the network has the lowest metric values. The cluster will honor this override and find the network with the next lowest value to send this type of traffic :
- In the Failover Cluster Manager snap-in, if the cluster that you want to configure is not displayed, in the console tree, right-click Failover Cluster Manager, click Manage a Cluster, and then select or specify the cluster that you want.
- Select Properties
- Change the radio buttons or checkboxes.
Option 2 (exclusively for “Live Migration Traffic”) :
To configure a cluster network for live migration:
- In the Failover Cluster Manager snap-in, if the cluster that you want to configure is not displayed, in the console tree, right-click Failover Cluster Manager, click Manage a Cluster, and then select or specify the cluster that you want.
- Expand Services and applications.
- In the console tree (on the left), select the clustered virtual machine for which you want to configure the network for live migration.
- Right-click the virtual machine resource displayed in the center pane (not on the left), and then click Properties.

- Click the Network for live migration tab, and select one or more cluster networks to use for live migration. Use the buttons on the right to move the cluster networks up or down to ensure that a private cluster network is the most preferred. The default preference order is as follows: networks that have no default gateway should be located first; networks that are used by cluster shared volumes and cluster traffic should be located last.Live migration will be attempted in the order of the networks specified in the list of cluster networks. If the connection to the destination node using the first network is not successful, the next network in the list is used until the complete list is exhausted, or there is a successful connection to the destination node using one of the networks.
Note : You don’t need to perform this action as per VM basis. When you configure a network for live migration for a specific virtual machine, the setting is global and therefore applies to all virtual machines.

Some other interesting articles:
http://technet.microsoft.com/en-us/library/dd446679(WS.10).aspx
http://blogs.technet.com/b/vishwa/archive/2011/02/01/tuning-scvmm-for-vdi-deployments.aspx
http://blogs.msdn.com/b/clustering/archive/2011/06/17/10176338.aspx
I am Speaking at Teched Australia 2011
I am absolutely thrilled to announce I will be presenting the following two sessions at Tech.Ed Australia 2011 :
| SCVMM 2012: Deployment, Planning, Upgrade
This session provides a scenario rich detailed walk through of VMM 2012 deployment, planning, and upgrade scenarios. Come and learn how to best plan your next VMM rollout |
| SCVMM 2012 Fabric Lifecycle: Networking and Storage
This session provides a scenario rich detailed walk through of new and more robust networking and storage features in VMM 2012. In this session you will learn how to discover, configure, and provision networking |
Came along! It will be an excellent session.
Tech.Ed Australia 2011 is on the Gold Coast between the 30th August and the 2nd September, registrations are now open. Find out more at http://australia.msteched.com/
Validate SCSI Device Vital Product Data (VPD) test fails after you install W2008 R2 SP1
If you found this error :” Failed to get SCSI page 83h VPD descriptors for cluster disk
<number> from <node name> status 2″ after applying SP1 to your W2008R2 cluster, Microsoft has released a fix for it.
The List Potential Cluster Disks storage validation test may display a warning message that resembles the following: “Disk with identifier <value> has a Persistent Reservation on it. The disk might be part of some other cluster. Removing the disk from validation set”
The hotfix resolves an issue in which the storage test incorrectly runs on disks that are online and not in the Available Storage group.
More details:
You configure a failover cluster that has three or more nodes that are running Windows Server 2008 R2 Service Pack 1 (SP1).
You have cluster disks that are configured in groups other than the Available Storage group or that are used for Cluster Shared Volumes (CSV).
These disks are online when you run the Validate SCSI Device Vital Product Data (VPD) test or the List Potential Cluster Disks storage validation test
More info : http://support.microsoft.com/kb/2531907
Plan your organization’s migration to a private cloud with the Hyper-V Cloud Fast Track Assessment!
Use the MAP Toolkit to plan your organization’s migration to a private cloud with the Hyper-V Cloud Fast Track Assessment!
New MAP features to:
- Build portfolios of web applications and databases to migrate to Windows Azure and SQL Azure.
- Assess your environment’s readiness for Office 365 or Internet Explorer 9
- Identify and migrate databases from competing platforms like Oracle and MySQL to Microsoft SQL Server.
- Consolidate your servers on to Hyper-V Cloud Fast Track Infrastructures
The beta of the MAP Toolkit v6.0 is now available. To get involved in the beta program
https://connect.microsoft.com/